Security
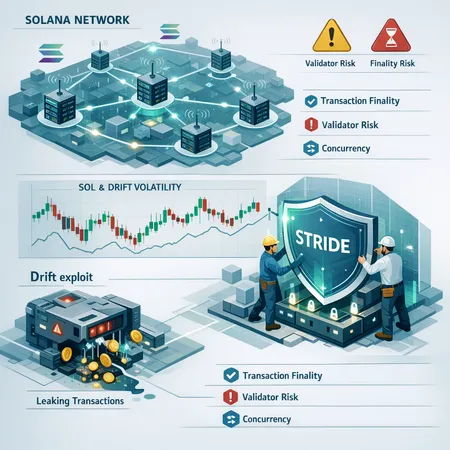
A deep dive into what the Drift exploit revealed about Solana's architecture, how the Solana Foundation’s STRIDE programme aims to reduce repeat incidents, and what this means for SOL price and trader behavior. Actionable recommendations for DeFi teams and users building on Solana are included.
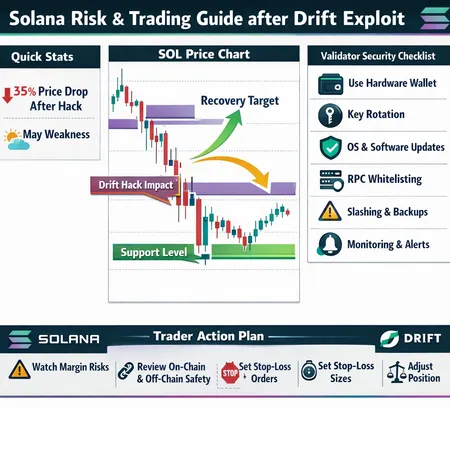
A concise roadmap for traders and node operators to quantify the short-term SOL price damage from the Drift exploit, map likely support/resistance, and implement on-chain and operational risk controls.
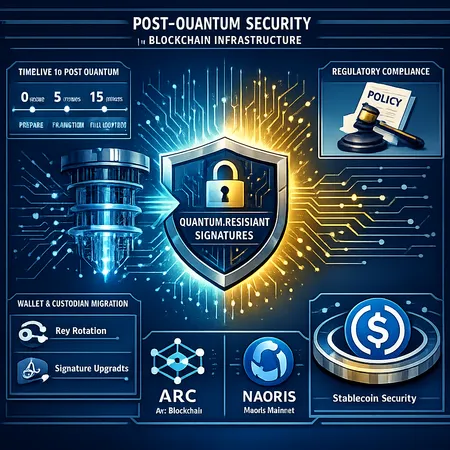
Quantum computers will reshape cryptographic risk models; this analysis explains why stablecoin rails and national-security-conscious blockchains are prioritizing post-quantum signatures now, with practical timelines, migration strategies, and policy implications. Case studies: Circle’s ARC and the Naoris mainnet launch.

A detailed post-mortem of the April 1 Drift Protocol hack: reconstructed attack chain, how social engineering and in-person tactics enabled months-long infiltration, evidence tying the operation to North Korean actors, and a practical checklist for DeFi risk teams.
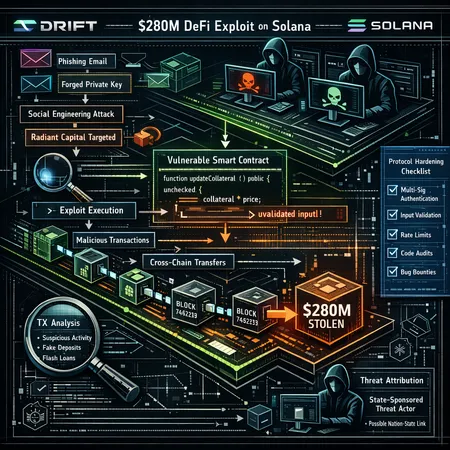
A deep post‑mortem of the $280M Drift Protocol exploit on Solana that reconstructs a months‑long intrusion, traces ties to prior Radiant Capital actors, and lays out prioritized defenses DeFi engineers should implement now.
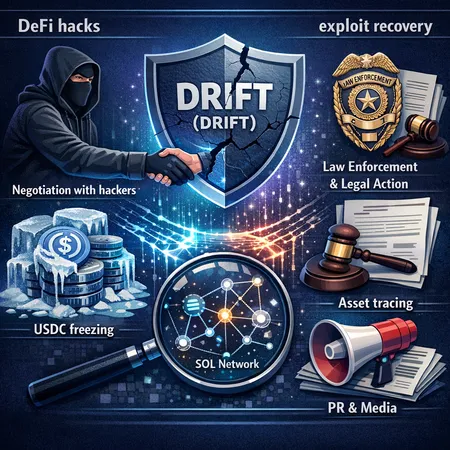
The Drift exploit exposed a shifting DeFi incident-response landscape: teams are weighing negotiations with alleged DPRK-linked attackers, stablecoin freezing limits, and the practical limits of on-chain recovery. This article outlines a pragmatic, legally informed playbook for protocol teams, security leads, and counsel.
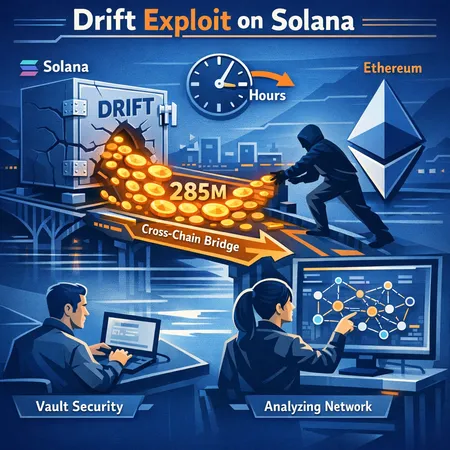
The $285M drain of Drift Protocol on Solana exposed critical cross‑chain and vault risks: attackers moved fast, bridged to Ethereum within hours, and amplified systemic exposure. This article reconstructs the likely attack flow, analyzes attacker behaviour, assesses implications for Solana DEX security and cross‑chain risk, and offers practical engineering and governance mitigations.
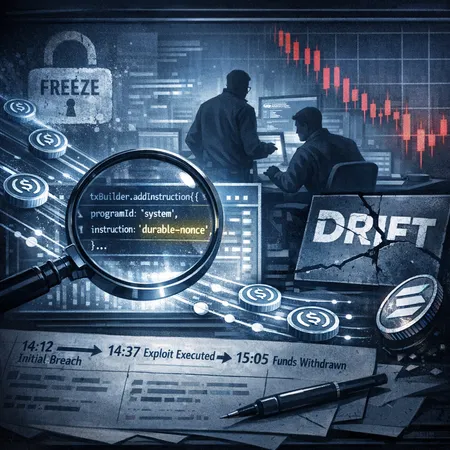
A forensic reconstruction of the Drift exploit on Solana: how a durable‑nonce attack let roughly $280–300M in USDC move, why transfers weren’t quickly frozen, the immediate SOL price and liquidity fallout, and what this means for DeFi security on high‑throughput L1s.
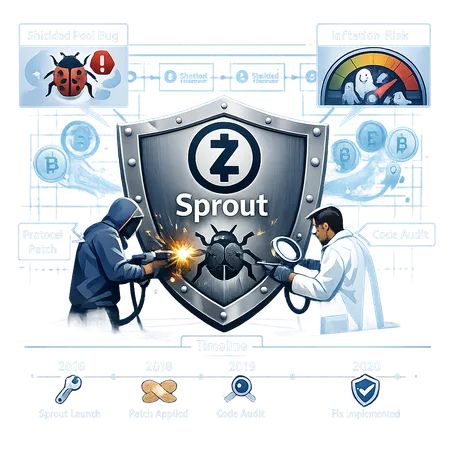
Zcash patched a critical Sprout shielded-pool bug that could have allowed forged shielded transactions and hidden inflation. This explainer breaks down the mechanics, the patch, the timeline, and practical recommendations for security engineers and ZEC holders.
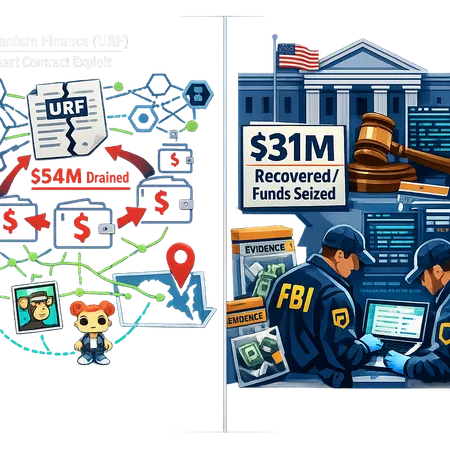
An investigative explainer on the Uranium Finance (URF) exploits, the U.S. revival of the case, a $31M crypto seizure, and forensic and legal lessons for DeFi teams. Practical steps for protocols to reduce exposure and improve recovery readiness are included.
DeFi
All DeFi postsBitcoin
All Bitcoin postsSecurity
All Security posts- Solana Risk Assessment After the Drift $285M Exploit: Price Damage, Supports, and Actionable Trading & Validator Controls
- Preparing for the Quantum Era: Post-Quantum Security for Stablecoin Rails — Arc & Naoris Case Studies
- Inside the April 1 Drift Protocol Hack: Reconstruction, North Korea Links, and a DeFi Security Playbook