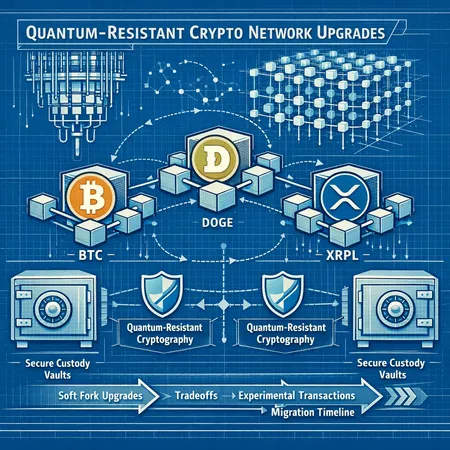
Quantum‑Resistant Upgrades for BTC, DOGE and XRPL: What Custodians Need to Know
Summary
Why "quantum‑resistant" matters today
The phrase quantum‑resistant is often used as shorthand, but for engineers and custody teams it must be operationalized: it means deploying cryptographic schemes or operational patterns that keep funds safe from exploitation by adversaries with large quantum computers capable of running Shor's algorithm (which can break widely used public‑key schemes such as secp256k1 and Ed25519).
It's important to be explicit about two realities: first, large fault‑tolerant quantum computers capable of breaking ECC are not here yet; second, key material exposed today can be harvested and stored by adversaries for future decryption, so systems with repeated public key reuse or long‑lived on‑chain exposure are at risk now. The right response is a combination of crypto upgrades (PQC or hybrid) and operational controls (key rotation, address hygiene, custody process changes).
Practical cryptography options
At a high level there are three practical directions:
- Adopt a standardized post‑quantum scheme (or a hybrid scheme combining a classical signature + PQC signature) — options include lattice‑based signatures like CRYSTALS‑Dilithium, stateless or stateful hash‑based signatures (SPHINCS+, XMSS/LMS), or other NIST finalists. Hybrid approaches hedge against future algorithm failures.
- Use one‑time or limited‑use keys and avoid long‑term reuse patterns (reduces harvest‑now, decrypt‑later risk).
- Architectural changes and scripts that reduce the on‑chain lifetime of public keys (e.g., pay‑to‑pubkeyhash patterns that minimize exposure).
Each choice has tradeoffs: signature sizes, verification costs, library maturity, hardware wallet support and standards compliance. Those tradeoffs shape the next sections on network‑specific proposals.
Bitcoin: the recent GitHub workaround and tradeoffs
A recent research implementation posted to GitHub and covered in reporting proposes a non‑soft‑fork workaround to introduce quantum‑safe spending constructs for Bitcoin without requiring a network soft‑fork. The summary idea is to create spending constructions that place a heavier reliance on off‑chain or preimage‑style mechanisms and allow nodes to accept quantum‑safe spends based on alternative validation data.
DailyCoin's coverage of the GitHub project lays out the design rationale and demonstrates how such a path reduces short‑term protocol disruption while enabling some wallets to opt into quantum‑resistant outputs: dailycoin.com GitHub workaround.
Why a no‑soft‑fork approach?
Hard or soft forks in Bitcoin are politically and technically costly. A non‑soft‑fork workaround aims to:
- Let wallets and custodians migrate without waiting for broad consensus or an activation window.
- Avoid splitting the UTXO set or imposing new consensus rules that older nodes can't follow.
But the approach is not free. Key tradeoffs include:
- Security model complexity: Non‑uniform adoption increases the surface for user errors; mixed output types mean some UTXOs remain classically vulnerable.
- Interoperability: Wallets, hardware devices, and services must explicitly support the new constructs, or funds may become awkward to spend.
- Limited guarantees: Because it's not a consensus rule, enforcement depends on policy and client support — not the innate safety of the chain.
Specific technical considerations for BTC engineers
- Script expressivity: Bitcoin's scripting and Taproot/Tapscript afford new flexibility (e.g., MuSig2, adaptor signatures) but integrating PQC primitives requires careful design to avoid bloating block validation time.
- Signature size and block limits: Many PQC schemes produce larger signatures, which affect fee economics and block weight. Hybrid signatures are especially heavy.
- Multisig and custody: Multisig setups complicate migration; approaches that change public key formats can force re‑construction of multisig wallets.
- Lightning and layer‑2 implications: Off‑chain protocols that rely on classical signature assumptions must be updated coherently, else funds held in channels could be at risk.
For many traders, Bitcoin remains the primary market bellwether; engineering teams should weigh the GitHub workaround as an intermediate mitigation — useful for reducing exposure quickly, but not necessarily a final, long‑term standard.
Dogecoin: experimental quantum‑resistant transactions
Dogecoin core contributors and engineers have been reported experimenting with quantum‑resistant transaction formats and prototype implementations. U.Today summarized current engineering work and commentary from Dogecoin engineers outlining efforts to test quantum‑resistant transactions on testnets and code branches: Dogecoin experiments with quantum‑resistant transactions.
What Dogecoin experiments show
- Dogecoin's engineering culture is pragmatic: prototypes focus on proving feasibility and measuring performance impacts rather than immediately pushing a mainnet activation.
- Testing tends to emphasize backward compatibility and low‑friction wallet migration paths so that exchanges and custodians can opt in gradually.
- Engineers are experimenting with hybrid signature schemes and transaction wrappers that allow a node or wallet to produce a classical signature plus a PQC signature together, easing interoperability.
The Dogecoin work is a useful case study: it demonstrates how an indie chain with a smaller developer surface area can rapidly prototype and test migration approaches — but it also highlights the same three friction points: signature size, client support, and custody migration logistics.
For teams tracking experimental work, following Dogecoin labs and testnets provides early signals about practical performance and UX tradeoffs.
XRPL: "only 0.03% vulnerable" — what that means for custodians
Recent analysis on XRPL suggests that only a very small portion of the circulating XRP supply is currently exposed to quantum key‑breaking vulnerability; Finbold reported a figure of approximately 0.03% being vulnerable today: Finbold XRPL quantum vulnerability.
Interpreting the statistic
That low percentage can come from several operational realities on XRPL:
- A substantial portion of holdings may be in addresses that use key types or custody arrangements that minimize on‑chain public‑key exposure.
- Many institutional cold wallets keep keys offline or use hardware security modules (HSMs) and multi‑party computation (MPC), which lowers practical harvestability.
- XRPL supports both secp256k1 and Ed25519; depending on how addresses are used and rotated, some accounts are intrinsically less exposed.
For custodians this number changes the calculus. If only a tiny fraction of supply is currently vulnerable, migration can be prioritized and staged rather than pushed as an immediate emergency. But beware: the low current exposure does not mean future immunity — as wallets move funds or as holding patterns change, exposure can grow.
Custodial implications on XRPL
- Prioritization: Custodians should identify which accounts correspond to the 0.03% (or similar vulnerable pools) and treat them as high priority for rotation or hybridization.
- Cost/benefit: Large‑scale migration on XRPL might be less urgent and more surgical than for UTXO‑based chains, but it still requires testing across client libraries and HSMs.
- Policy design: XRPL operators can design staged migrations for high‑risk addresses first, then broader adoption once PQC standards and libraries reach production quality.
Timelines and migration complexity
There is no single, correct timeline; instead, teams should align their plans to two external signals:
- PQC standardization and library maturity (NIST progress and well‑audited implementations).
- The organization's risk tolerance and the potential for key‑harvesting by adversaries.
A practical staging plan for custody teams might look like this:
- Immediate (0–6 months): inventory all keys and addresses, identify high‑value and highly exposed UTXOs/accounts, enable address hygiene (avoid reuse), and update threat models. Begin vendor engagement (HSM/MPC/ledger) and test PQC implementations in lab.
- Near term (6–24 months): deploy hybrid signatures in wallet software where feasible; test migrations on testnets and with canary sets of low‑value funds; update signing infrastructure to handle larger signatures and new algorithms; perform audits and pen tests.
- Medium term (24–48 months): gradual mainnet migration for high‑value accounts, full multisig re‑keying, and deprecation plans for legacy key types. Coordinate with exchanges, counterparties and standards groups for network activation windows if consensus changes are required.
- Long term (48+ months): full transition to PQC or hybrid by default once standards and implementations prove robust.
Complexity drivers include the chain architecture (UTXO vs account model), multisig setups, smart contracts and layer‑2 dependencies, and the need to update hardware wallets and HSM firmware.
Recommended steps for exchanges and custody providers
Below is a prioritized checklist for engineering and security leads preparing for post‑quantum risk.
1) Asset and key inventory (Immediate)
- Map every key type in use (secp256k1, Ed25519, other).
- Tag accounts/UTXOs by exposure level and business impact.
- Track third‑party dependencies (wallet providers, HSM vendors, MPC providers) and their PQ preparedness.
2) Threat model and policy updates (Immediate)
- Update risk models to include harvest‑now, decrypt‑later scenarios.
- Define acceptable exposure thresholds per asset (e.g., BTC vaults vs hot wallets).
- Engage legal/insurance teams to align policy language with migration plans.
3) Lab testing of PQC and hybrid schemes (0–12 months)
- Implement hybrid signature prototypes in a controlled environment.
- Measure signature sizes, verification cost, network impact and wallet UX.
- Run interop tests with hardware wallets and HSMs; coordinate firmware updates.
4) Staged migration and canary releases (6–24 months)
- Migrate low‑value funds and simple wallets first; perform live drills for recovery and key‑rotation.
- For Bitcoin, consider the GitHub workaround as an intermediate step to reduce exposure while the community converges on a standard. See the GitHub research summary at DailyCoin for a quick reference: dailycoin.com GitHub workaround.
5) Coordination and communication (ongoing)
- Coordinate with exchanges, counterparties, and major custody customers to synchronize migration windows.
- Publish migration and rollback procedures publicly for transparency and to avoid accidental replay or incompatibility issues.
6) Insurance and compliance adjustments (near term)
- Revisit insurance coverage for cryptographic compromise and supply chain risk.
- Update compliance artifacts to reflect key rotation schedules and PQC adoption timelines.
7) Operationalize ongoing monitoring (ongoing)
- Monitor PQC standardization (NIST updates), research breakthroughs, and public testnets for regressions.
- Track on‑chain indicators of harvest activity (new scanners might be able to see mass public‑key collection attempts).
Engineering pitfalls to avoid
- Don’t wait for 100% certainty: harvest‑now risks make proactive mitigation prudent.
- Avoid half‑measures that create management complexity without reducing exposure (e.g., ad hoc address formats without robust wallet support).
- Don’t ignore UX: if custody clients can’t produce or verify hybrid signatures easily, adoption stalls.
Bitlet.app and other custody tools are already evaluating hybrid approaches in lab environments; integrating such solutions early reduces later operational churn.
Conclusion — a risk‑managed, staged approach
Quantum‑resistant upgrades are less about a single technical silver bullet and more about a disciplined program: inventory, threat modeling, lab tests, staged migration and vendor coordination. The recent Bitcoin GitHub workaround provides a plausible short‑term mitigation without a soft‑fork, Dogecoin's experiments show how pragmatic prototyping can de‑risk real‑world performance questions, and XRPL's low current vulnerability statistic lets custodians prioritize surgical migrations.
For custody and exchange operators: treat the problem as urgent but manageable. Start now with inventories and lab work, adopt hybrid schemes where possible, and plan multi‑year staged migrations aligned with PQC standardization and ecosystem readiness.
Sources
- DailyCoin — Quantum‑safe Bitcoin workaround and GitHub research: https://dailycoin.com/quantum-safe-bitcoin-no-soft-fork-a-new-workaround-hits-github/
- U.Today — Dogecoin experiments with quantum‑resistant transactions: https://u.today/dogecoin-experiments-with-quantum-resistant-transactions-doge-engineer-weighs-in?utm_source=snapi
- Finbold — XRPL vulnerability statistic (0.03%): https://finbold.com/only-0-03-of-xrp-supply-is-vulnerable-to-quantum-threats/?utm_source=snapi


