Quantum‑Resistant Crypto: Where BTC, DOGE and XRP Stand and What Product Teams Should Do

Summary
Executive snapshot
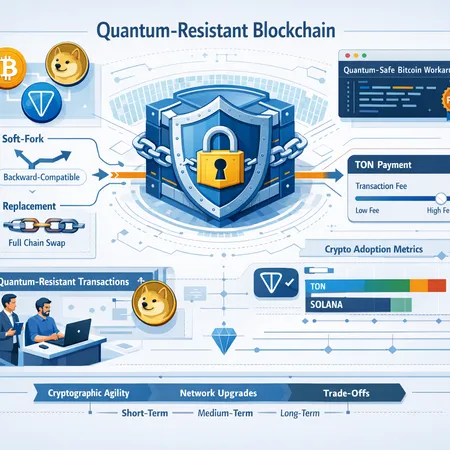
Quantum computers that can break ECDSA or Schnorr would threaten widely used cryptocurrency keys, but capable machines are not yet here. That said, the ecosystem has moved from “ignore it” to “plan and prototype.” Recent work ranges from a GitHub‑hosted Bitcoin workaround that aims to introduce quantum‑safe options without a soft fork to Dogecoin developer experiments with quantum‑resistant transaction designs, while the XRP Ledger today reports a very small portion of its supply as vulnerable (roughly 0.03%). For product managers and security teams, the question is not whether to act but how quickly and which mitigations to prioritize.
Where the major projects stand
Below I summarize the current posture for BTC, DOGE and XRP and what those positions mean for operations and product planning.
Bitcoin (BTC): a conservative ecosystem with new workaround proposals
Bitcoin’s community has historically preferred minimal consensus changes and long testing cycles. That conservatism slows rapid protocol change but encourages rigorous design. A recent GitHub workaround—reported in technical coverage—proposes ways to offer quantum‑safe spending options without requiring a network soft fork; the idea focuses on wallet and script‑level techniques that let users opt into post‑quantum keys while keeping legacy consensus untouched (see the writeup on the workaround for technical context) quantum‑safe Bitcoin no soft fork.
What this means in practice: Bitcoin can be incrementally hardened by wallet software and custodians first, then by coordinated changes if and when a standard emerges. For many teams, that implies planning for layered rollouts and prioritizing tooling that supports hybrid (classical + post‑quantum) spending policies. For many traders, Bitcoin remains the primary market bellwether, so operational continuity during any transition is paramount.
Dogecoin (DOGE): active experiments at the protocol and client level
Dogecoin developers and engineers have started prototyping post‑quantum transaction ideas and signing schemes, with public discussion and experiments aimed at assessing feasibility and performance tradeoffs in a live testnet environment. Coverage of these experiments highlights early design choices and community feedback loops around signature families and transaction formats (see the developer discussion and experiments) Dogecoin experiments.
Operational takeaway: Dogecoin’s faster release cadence and lighter governance make it a useful proving ground for approaches that may later be ported to more conservative chains. Product teams evaluating DOGE should engage with client releases and testnets early to validate backward compatibility and client library support.
XRP Ledger (XRP): limited current exposure but not zero risk
Analysis tied to the XRP Ledger suggests only about 0.03% of the total XRP supply is currently in accounts that are demonstrably vulnerable to quantum key‑stealing attacks, typically because an account’s public key has been exposed and the corresponding private key could be attacked in principle (analysis reported by Finbold) XRP exposure.
Interpretation: XRP’s current on‑ledger posture looks healthier than many chains, but this is a snapshot — future application patterns (e.g., new smart contract or signing schemes) could change exposure. Custodians and exchanges should still run inventories and flag accounts that have revealed public keys.
Short technical primer: post‑quantum signatures and tradeoffs
If you’re a product manager building a migration plan, you need to understand the simple tradeoffs between candidate post‑quantum (PQ) signature families.
Why classical signatures are vulnerable
Current mainstream signatures (ECDSA, Schnorr) rely on discrete log problems over elliptic curves. A large, fault‑tolerant quantum computer running Shor’s algorithm would efficiently recover private keys from public keys. The practical implication: any address where the public key has been revealed (for example, after spending) becomes a target if a capable quantum attacker can act before funds are moved under post‑quantum protection.
Main PQ signature families and properties
- Hash‑based (e.g., SPHINCS+): extremely conservative security assumptions and well‑studied. Often produce larger signatures and may be slower, but are stateless variants exist. SPHINCS+ was selected by NIST as a standard‑ready scheme.\
- Lattice‑based (e.g., CRYSTALS‑Dilithium, Falcon): compact signatures and high performance; widely favored for near‑term deployment. Dilithium was among NIST’s signature finalists.\
- Multivariate and code‑based schemes: have niche uses and varied performance/size tradeoffs.\
Key practical tradeoffs: signature size, verification cost, key size, and whether a scheme is stateful (requires careful one‑time use bookkeeping) or stateless. For blockchains, signature size and verification throughput directly affect fees and block validation costs.
Hybrid signing: the pragmatic bridge
Most realistic migration plans use hybrid signatures: transactions carry both a classical and a PQ signature, and spending requires either of two policies (e.g., both signatures required or PQ signature accepted as alternative). Hybrid approaches provide crypto agility while easing migration risk.
Practical implications for wallets, exchanges and custody providers
Quantum risk is a governance and operations problem as much as a cryptography problem. Below are near‑term actions and design decisions for different custodial and non‑custodial roles.
Wallets (software and hardware)
- Avoid address reuse. Public keys should be revealed as little as possible; prefer one‑time use addresses where feasible.\
- Add support for post‑quantum key generation and hybrid signing in wallet libraries and hardware device firmware. Start with testnet implementations and vendor coordination.\
- Expose migration workflows: allow users to create PQ receiving addresses and guide funds migration for any at‑risk keys.\
- UX matters: explain why a longer signature or slightly slower signing is acceptable for improved resilience.
Exchanges and custodians
- Inventory and classify keys by revealed public key status. The XRP analysis showing ~0.03% exposure is an example of the kind of audit you should run for your supported assets XRP exposure.\
- Prioritize migration of funds held in addresses with exposed public keys. Implement phased migrations to post‑quantum or hybrid addresses with rigorous testing.\
- Design key‑rotation and recovery playbooks. Offline key generation, multi‑party computation (MPC) and multi‑signature schemes can reduce single‑point risks during migration.\
- Coordinate with upstream node implementations: if Bitcoin adopts wallet‑level workarounds (for example, the GitHub proposals), exchanges will need to update signing software to interoperate quantum‑safe workaround.
Custody providers and institutional ops
- Test and certify PQ key storage solutions and establish attestation processes for hardware modules and MPC vendors.\
- Simulate incident response for a hypothetical rapid quantum breakthrough: rapid de‑posits and withdrawals, mass migrations, fee market congestion — practice the operational choreography.\
- Ensure legal and compliance teams understand the migration implications of on‑chain movements and user notifications.
Adoption timeline: realistic milestones and probabilities
Below is a pragmatic timeline with rough probability bands for wide deployment across major chains. These are informed estimates, not predictions.
Near term (0–2 years): increased prototyping and wallet‑level tooling, more testnet releases. High probability. We already see Dogecoin experiments and GitHub proposals for Bitcoin‑adjacent approaches Dogecoin experiments quantum‑safe workaround.
Medium term (2–5 years): adoption of hybrid signing schemes in major wallets and custodial platforms, selective protocol upgrades where necessary (soft forks or versioned transaction formats). Moderate probability — dependent on standardization progress and the emergence of practical quantum threats.
Long term (5+ years): full rollouts of protocol‑level support and wide adoption of PQ signatures across major chains. Lower probability in that exact window — contingent on both advances in quantum computing and consensus choices in each community.
These windows reflect both technical work needed to standardize PQ primitives (e.g., NIST activity) and the governance pace of each chain.
What product managers and security‑minded users should do today
- Inventory and classify: run a thorough audit to find accounts that have exposed public keys across BTC, DOGE and XRP holdings. Use the XRP 0.03% vulnerability analysis as a model for this sort of snapshot XRP exposure.\
- Reduce address reuse immediately and enforce best practices in new product flows.\
- Pilot hybrid signatures in non‑critical environments and testnets. Encourage hardware wallet vendors and custodial signers to support hybrid schemes.\
- Design migration mechanics and rehearse them: for large custodial balances, migration windows, fee assumptions, and user communications must be prepared.\
- Track upstream protocol and client proposals; for Bitcoin teams, watch the GitHub workaround discussions and be ready to upgrade signing stacks when tested implementations stabilize quantum‑safe workaround.\
- Communicate with users: provide clear guidance about why these steps matter, and what actions (if any) users need to take now. For many retail users the practical advice is simple — don’t reuse addresses and prefer custody solutions with active PQ roadmaps. Product teams at Bitlet.app and elsewhere should surface migration timelines and tooling as features, not just engineering tasks.
Conclusion: urgency without panic
Quantum‑resistant cryptography is now a technical program, not a thought experiment. There’s no immediate need for emergency mass migrations — the timelines and current exposure numbers (for example, XRP’s low present vulnerability) justify measured planning — but there is clear practical value in early prototyping, inventorying risk, and building migration and UX plans. By adopting hybrid signing patterns, avoiding address reuse, and coordinating across wallets, exchanges and custody providers, teams can materially increase crypto resilience long before a quantum machine becomes an existential threat.
Sources
- "Quantum‑safe Bitcoin no soft fork: a new workaround hits GitHub" — DailyCoin: https://dailycoin.com/quantum-safe-bitcoin-no-soft-fork-a-new-workaround-hits-github/
- "Dogecoin experiments with quantum‑resistant transactions" — U.Today: https://u.today/dogecoin-experiments-with-quantum-resistant-transactions-doge-engineer-weighs-in?utm_source=snapi
- "Only 0.03% of XRP supply is vulnerable to quantum threats" — Finbold: https://finbold.com/only-0-03-of-xrp-supply-is-vulnerable-to-quantum-threats/?utm_source=snapi