Inside the $285M Drift Protocol Heist: Attack Flow, Fast Bridging, and How DeFi Teams Should Harden Vaults
Summary
Executive recap
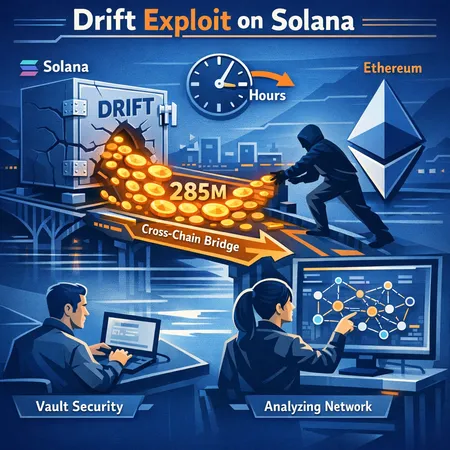
In Q1 2026 Drift Protocol, a prominent Solana native derivatives DEX, was drained of roughly $285M in what reporting calls one of the largest DeFi exploits of the year. Public coverage from several outlets reconstructed a rapid sequence: an on‑chain exploit on Solana, quick swaps into liquid assets and stablecoins, and bridging of most proceeds to Ethereum within hours, complicating recovery and forensic tracing. Early reporting suggests the operation was sophisticated and highly time‑sensitive, with attackers prioritizing speed over stealth.
For readers focused on engineering and risk: this is a reminder that vault logic, clearinghouse invariants, and bridge assumptions are a single attack surface. Many teams building on Solana and monitoring DeFi risk metrics will want both a technical reconstruction and prescriptive hardening steps.
What the public timeline and reports tell us
Published reporting provides a compact but consistent outline of events. News outlets reported a roughly $285M outflow attributed to Drift Protocol; coverage characterizes it as a highly sophisticated operation that hit a Solana DEX and had immediate downstream effects on liquidity and markets. The Unchained Crypto story highlights the speed of bridging to Ethereum and notes that funds were moved across chains within hours. The initial, detailed report and chain analysis capture the size and routing of funds as they exited Solana into other chains and services.
- NewsBTC framed the exploit as a high‑sophistication attack that materially impacted the Solana DEX ecosystem and liquidity pools.
- Unchained Crypto documented that the attacker rapidly bridged assets to Ethereum soon after extraction, limiting the window for recovery or on‑chain intervention.
- Bitcoin.com provided the initial detailed report outlining the timeline and scale.
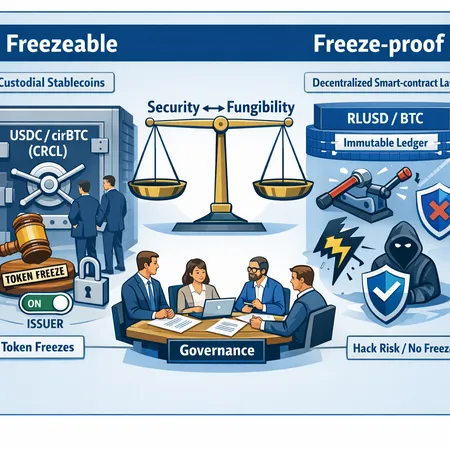
- CoinPedia connected the hack to wider industry debates (for example, the limits of freezeable vs freeze‑proof stablecoins and what operational options custodians have in an emergency).
Taken together, these sources indicate three key phases: initial exploit on Solana, asset conversion and staging, and cross‑chain bridge outflows to Ethereum. For detailed reporting see the reconstructed timelines in the cited coverage: NewsBTC, Unchained Crypto, Bitcoin.com, and CoinPedia.
Reconstructing the likely attack flow
Below is a conservative reconstruction built from on‑chain signals reported publicly and standard attacker tradecraft observed in previous DeFi heists. This is not an authoritative forensics report, but a practical model teams can use to stress test logic and alerting.
Initial breach of vault/clearing logic
- The attacker exploited a vulnerability in Drift’s vault/clearinghouse code path that allowed unauthorized value extraction or the bypassing of expected invariants (e.g., undercollateralized position settlement, improper state transition checks, or broken access control on withdrawal paths).
- Targeting on‑chain accounting (margins, collateralization ratios, settlement functions) is a common pattern for derivatives DEX exploits because it yields high leverage on protocol funds.
Rapid consolidation and liquidity harvesting
- Exploiter converts a portion of stolen assets into the most liquid on‑chain assets available (SOL, USDC, USDT) via DEXes or concentrated liquidity pools to enable fast transfer.
- Funds are split into many wallets to avoid immediate large slippage and to blend routing strategies (DEX swaps, concentrated limit fills, and direct transfers to bridge contracts).
Bridge staging and fast cross‑chain transfer
- Attackers stage funds into bridgeable tokens and interact with multiple bridge contracts to send value to Ethereum and other chains. Reports indicate most funds were bridged to Ethereum within hours, a sign that the attacker prioritized leaving the Solana security perimeter quickly.
- In practice attackers use whichever bridge offers immediate liquidity and low censorship risk. Rapid bridging reduces the efficacy of on‑chain freeze or custodial interventions tied to chain‑specific controls.
Post‑bridge obfuscation (mixing, swaps, layer‑2s)
- Once on Ethereum, proceeds are commonly subject to additional swapping, splitting, and moving through privacy‑oriented services or decentralized mixers. That step further complicates recovery and increases the odds of converting into fiat or off‑rampable assets.
Attacker behaviour: why speed mattered
The swift bridging observed in this case is now familiar from prior high‑value attacks: speed is a tactical choice. A fast exit reduces the window for:
- On‑chain community coordination or pausing of bridges and markets.
- Centralized custodians or stablecoin issuers from applying freezes or blacklists to flagged addresses.
- Liquidity takedown by white hats or negotiators trying to re‑acquire funds.
Unchained’s reporting emphasizes this quick cross‑chain movement. Speed also means attackers accept higher transaction costs and some slippage to safeguard against countermeasures. From a defender’s viewpoint, the implication is clear: mitigating damage requires a cross‑chain lens and preparedness to act within minutes, not hours.
Implications for Solana DEX security and cross‑chain risk
This exploit surfaces a few structural vulnerabilities relevant to security teams and institutional risk managers:
- Single‑chain tackiness: When core risk logic and settlement are completely on a single chain (Solana here), a protocol‑level compromise can instantly threaten any assets that are cross‑collateralized or exposed in vaults.
- Bridge amplification: Bridges convert a local compromise into a global one. A single unchecked bridge hop can turn a Solana incident into a multichain incident in under an hour.
- Operational limitations: Some custodians and stablecoin issuers may have limited ability or willingness to intervene, especially when funds rapidly move across jurisdictions and chains (CoinPedia discusses the freezeable vs freeze‑proof stablecoin tradeoffs in this context).
For institutional counterparties, the lesson is that custody risk is not only about cold wallets or multisig; it’s also about how protocols execute state transitions, how quickly assets can be withdrawn and bridged, and the controls across each involved system.
Engineering mitigations: hardening vaults, bridges, and clearing logic
Below are concrete engineering controls security teams should prioritize. Many are low‑regret and compatible with continued composability.
- Vault invariants and hardened checks
- Implement explicit, audited invariant checks for all vault and clearinghouse transitions; fail closed if invariants do not hold. Use assertions that are both on‑chain and checked off‑chain in simulation tests.
- Deny direct withdrawals that bypass accounting paths. Route all value movements through a small set of vetted methods with access controls and time‑delay gates.
- Use bounded per‑tx withdrawal limits and global daily caps that cannot be bypassed without multisig‑level governance.
- Time delays and staged exits for high‑value ops
- Add configurable timelocks for large withdrawals or for operations that change treasury exposure (e.g., > X% of total TVL). Short delays (minutes to hours) can be enough for human or automated intervention.
- Combine timelocks with on‑chain event notifications to off‑chain incident response teams.
- Circuit breakers and automated sanity checks
- Implement real‑time sanity checks that monitor deviation from expected price, funding, and collateral ratios. Trigger circuit breakers when anomalies exceed thresholds.
- Circuit breakers should route to a secure multisig pause function that requires an offline quorum to resume.
- Bridge hardening and policy
- Avoid allowing arbitrary third‑party bridge interactions from critical vaults. Whitelist specific bridges, require a validator set or oracle confirmation for cross‑chain state, and limit per‑bridge transfer caps.
- Use delayed confirmation windows on minting of bridged assets or on high‑value incoming transfers originating from wrapped tokens.
- Least privilege and modular design
- Keep bridge adapters, liquidation modules, and treasury operations separated with minimal privileges. If one module is compromised, it should not enable arbitrary draining of unrelated vaults.
- Prefer upgradable patterns that preserve the ability to patch flaws but whose upgrades require multisig/quorum approval with enforced review periods.
- Testing and verification
- Adopt fuzzing, formal verification on critical invariants, and regular red‑team exercises that simulate bridge exits and large withdrawal scenarios.
- Respect supply chain risks: vet and pin dependency versions for runtime crates or packages used in the protocol.
Governance and operational mitigations
Engineering controls need governance glue. Recommendations:
- Emergency multisig and response playbooks: Maintain an accessible, rehearsed incident response plan and a well‑documented multisig setup that can act quickly. Ensure signers are geographically and institutionally diverse.
- Insurance and capital buffers: Maintain dedicated insurance funds and build relationships with market counterparties and insurers who understand cross‑chain exposures.
- Responsible disclosure & bounty programs: Keep an active bug‑bounty at market rates for critical net‑positive incentives.
- Transparent communication: Clear, honest updates to users and counterparties reduce panic and help coordinate white‑hat recovery if possible.
Detection and response playbook (practical steps)
When an exploit is suspected, teams should act on both detection and containment in parallel:
- Immediate detection signals
- Large unexpected outflows from vaults, anomalous settlement failures, or mass liquidation events.
- Pattern matching on transaction graphs: many small swaps followed by bridge contract interactions are red flags.
- Rapid containment steps (minutes to hours)
- Invoke multisig pause if available; notify bridge maintainers and request temporary halts or watchlist measures.
- Inform major CEXs and stablecoin issuers with on‑chain evidence and address lists; while not guaranteed, some institutions will block or freeze if actionable.
- Forensics and legal support
- Archive on‑chain data immediately and coordinate with chain analytics firms for tracing. Public reports suggest that fast cross‑chain bridging complicates tracing and necessitates immediate forensic engagement.
- Engage counsel early to assess legal or regulatory avenues to compel freezes or cooperation.
Insurance, market confidence, and the long arc
High‑value breaches like this one create a feedback loop: market counterparties tighten limits, insurers raise premiums, and institutional participants reassess integrations. Some of these effects are transient; others reshape product design. The event adds momentum to a few longer‑term shifts:
- Preference for bridge designs with stronger fraud proofs and delayed minting semantics.
- Increasing demand for on‑chain proofs, attested audits, and stronger operational guarantees from protocols used by institutions.
- Acceleration of vault design toward conservative defaults: per‑user limits, fewer infinite approvals, and safer liquidation logic.
Bitlet.app and other ecosystem tools that measure protocol exposure should surface cross‑chain flow risk as a first‑class metric to support institutional due diligence.
Concluding notes for security teams and risk leads
The Drift exploit is a stark reminder: the attack surface in DeFi now spans on‑chain invariants, cross‑module privileges, and the bridges that connect ecosystems. Defenses must be layered: rigorous engineering of vault and clearing logic; bridge and adapter constraints; quick operational playbooks; and governance that can act decisively under pressure.
No single control is a panacea; speed, diversity of controls, and rehearsed human processes matter most. Teams should treat cross‑chain flows as an operationally critical path and design for the possibility that attackers will try to exit to another chain within minutes.
Sources
- Initial detailed reporting and chain analysis on the extract size and timing (Bitcoin.com)
- Unchained Crypto: reporting on rapid bridging to Ethereum and actor attribution considerations
- NewsBTC: framing the exploit as a sophisticated operation and Solana DEX impact analysis
- CoinPedia: discussion connecting the attack to debates over freezeable vs freeze‑proof stablecoins and operational responses