Quantum Risk for Blockchains: Timeline, Why Cardano Scores Well, and a Practical Roadmap
Summary
Why Google Quantum AI’s paper matters for blockchain security
Google Quantum AI’s recent work reframed the technical conversation about how many qubits — and what quality of error correction — are required before a useful quantum attack against classical signature schemes becomes feasible. The paper does not say “today’s quantum machines break Bitcoin,” but it tightens the engineering roadmap: achievable qubit counts and improved error-correction approaches make a cryptanalytic threat a more plausible multi‑year engineering milestone than some older, conservative estimates suggested. For a concise journalist summary see Cryptoslate’s coverage of the paper here.
At a high level, the paper’s takeaways are: quantum attacks still demand large numbers of logical qubits and substantial physical‑qubit overhead for fault tolerance, but progress on error correction and architectural designs compresses those resource estimates. That means timelines that once looked like “many decades” may now plausibly be measured in years to a decade for well-funded adversaries — a point underscored by follow-ups warning the threat could arrive sooner than previously expected (see Coinpaper’s discussion here).
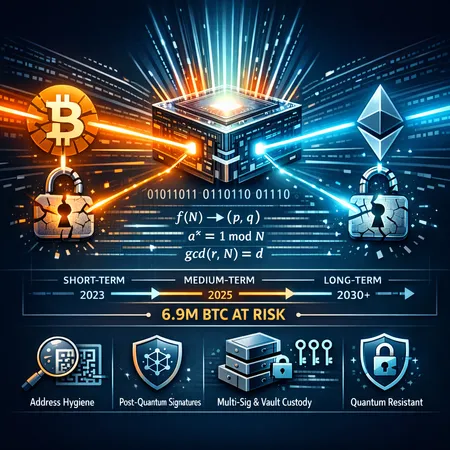
Translating qubit counts into practical timelines for blockchains
Security teams don’t work in logical qubits — they need to know which systems and assets are at risk now, in five years, and in a decade. The practical threat depends less on a single global quantum date and more on three operational realities:
- Whether a chain exposes public keys on-chain (account vs UTXO models).
- Where keys are stored (hot custodial wallets vs long-term cold storage).
- The ease with which the protocol can be upgraded to post‑quantum algorithms.
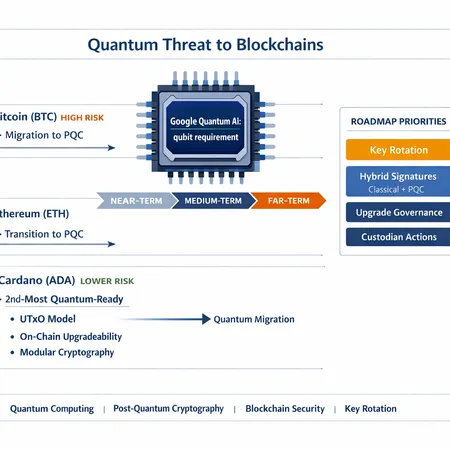
BTC (Bitcoin)
Bitcoin’s UTXO model and widespread use of pay-to-public-key-hash (P2PKH) historically reduced immediate exposure: many addresses reveal only a hash until coins are spent, so an attacker can’t attack a public key they don’t see. However, when a UTXO is spent the public key is revealed and that spending transaction becomes a short window of vulnerability — an attacker with a capable quantum device could try to derive the private key and broadcast a competing spend. That means coins already sitting in addresses with revealed public keys (or that will soon be spent) are the most at risk.
Longer term, if a sufficiently capable quantum adversary appears in the wild, custodians, exchanges and users would need to rotate keys and migrate funds. The good news: Bitcoin has a conservative upgrade path and many custodial setups already use multi‑sig and hardware security modules, which are useful bases for transition.
ETH (Ethereum)
Ethereum’s account model frequently exposes public keys by design during regular transactions, increasing the immediacy of the risk for active accounts. Smart contract wallets and DeFi positions that have interacted with contracts — especially those that maintain frequently used keys — are more exposed than cold, dormant addresses. Because of this, Ethereum users and protocols should treat the risk as more time-sensitive than for some UTXO-only setups.
ADA (Cardano)
Cardano recently popped up in rankings as one of the most ‘quantum-ready’ chains — a result of both its architectural choices and stated upgradeability roadmap. U.Today reported that Cardano was named second-most quantum-ready by Google’s analysis here. Why did Cardano score well? Two reasons stand out: stronger modularity in the protocol stack (making cryptographic primitives more replaceable) and governance/upgradability mechanisms that enable planned migrations without painful hard forks. Those qualities reduce the friction of post-quantum transitions compared with protocols that lack formalized, on-chain upgrade paths.
Why Cardano’s architecture makes post‑quantum migration easier
Cardano’s relative ranking is not magic; it’s architectural and organizational.
Cryptographic modularity: Protocols that keep signature, hashing, and consensus primitives in well‑defined layers can swap out algorithms with less invasive code churn. Cardano’s node implementation and formalized specifications make targeted cryptographic replacement more straightforward.
Upgrade governance: Cardano’s governance and upgrade model (including the ability to stage and test protocol changes) means community-driven migrations can be coordinated with a clear timeline, testnets and rollback plans — all critical when introducing new cryptography that must be scrutinized.
eUTXO model and address practices: While not immune, eUTXO and encouraged address hygiene (avoid reuse) reduce the surface of immediately exposed public keys compared with account-model chains.
Formal methods and engineering discipline: The project’s emphasis on formal verification and peer review accelerates safe deployment of high-risk changes like new signature schemes.
These architectural choices are instructive for other chains: agility, clear layering, and robust governance materially reduce migration risk.
Practical, prioritized roadmap for developers and custodians
Below is a prioritized, pragmatic plan focused on risk reduction and operational feasibility. Treat this as a living checklist: the order can change by asset criticality and exposure.
Priority 1 — Immediate (0–6 months): inventory, policies, and hot-wallet hygiene
- Perform a full key inventory: classify keys by exposure (hot custodial keys, staking operator keys, long-term cold keys) and by whether their public key has been revealed on-chain. Track which assets are held under keys with revealed public keys.
- Update custody and wallet policies: require minimal hot-wallet balances, increase cold storage usage, and enforce no-address-reuse where practical.
- Initiate urgent rotations for keys that are both hot and have exposed public keys. For custodians and exchanges (including platforms like Bitlet.app), moving critical funds to freshly generated keys and implementing multi-sig for hot funds reduces single-key attack surface.
Priority 2 — Short term (6–18 months): adopt hybrid signatures and hybrid verification
- Implement hybrid signatures in applications and SDKs: sign messages and transactions using both the classical algorithm (e.g., ECDSA/Ed25519) and a vetted post‑quantum algorithm (e.g., a NIST‑selected candidate when standardized). Verification must accept and validate both components.
- Roll out hybrid support in wallet libraries and client software first, then server-side validation. Hybrid schemes provide defense-in-depth: even if one algorithm falls, the other still protects assets during migration.
- For custodians, adopt threshold signing and multi‑party computation (MPC) where possible. PQ-resistant threshold schemes are an important mitigation as single-key compromise becomes catastrophic in a quantum world.
Priority 3 — Medium term (12–36 months): protocol upgrades, testnets and governance
- Prepare on-chain upgrade proposals and testnet exercises. Protocol teams should prototype post‑quantum signature verification at the consensus and mempool levels and measure performance and chain-state impacts.
- Use staged rollouts with strong telemetry: test across clients, stress test memory/CPU impacts, and evaluate signature size/fee consequences. Larger post‑quantum signatures can increase transaction sizes and affect fees; plan for those trade-offs.
- For chains with slower governance paths, define emergency upgrade procedures and off‑chain coordination plans — the goal is to avoid last-minute, rushed switches.
Priority 4 — Long term (2–5+ years): full cryptographic agility and deprecation plan
- Transition to NIST‑standardized post‑quantum algorithms or vetted hybrids once standards stabilize. Maintain cryptographic agility: keep the ability to swap algorithms without hard forks when possible.
- Sunset old algorithms with clear deprecation timelines and tooling to assist wallets/custodians in migrating keys and funds.
- Continue R&D into quantum-resistant key management, threshold PQC schemes and hardware acceleration for signature verification.
Operational recommendations by role
- Protocol engineers: build cryptographic agility into the client stack now — pluggable signature modules, feature flags for hybrid verification, and automated test suites.
- Custodians and exchanges: prioritize rotating hot and recently used keys now, deploy hybrid signing for deposit/withdrawal flows, and enforce multi-sig/MPC for high-value wallets.
- Security leads: run tabletop exercises simulating a large-scale quantum-capable adversary; test incident response for urgent rekeying and chain-upgrade scenarios.
Practical mitigations you can deploy today
- Avoid address reuse and minimize public key exposure on-chain.
- Use hardware wallets that support key rotation workflows and multi‑sig.
- Start hybrid signature adoption in SDKs and APIs used by wallets and custodial systems.
- Coordinate with protocol governance to schedule testnets for PQC migration — real upgrades are socio-technical events, not purely engineering tasks.
Final assessment: urgency without panic
Google’s paper shifts the calculus: the quantum threat is closer than some conservative forecasts implied, but it is not an immediate single‑day disaster. The right posture is proactive preparation: inventory and operational hardening today, hybrid and threshold mitigations in months, and coordinated protocol upgrades over the medium term. Chains with modular stacks and strong governance (as highlighted by Cardano’s ranking) will find migration less disruptive — a useful lesson for protocol architects.
For protocol engineers and security leads, the concrete next steps are clear: inventory keys, accelerate rotations for high‑exposure assets, implement hybrid signatures in client/server flows, and use governance channels to define upgrade roadmaps and testnets. Practical, prioritized action now buys time to adopt standards carefully later.
If you’re building migration plans for custodial services or protocol upgrades, treating post‑quantum readiness as part of your core security lifecycle is the most cost‑effective risk management you can do. Exchanges and custodians such as Bitlet.app will need to coordinate these steps across product, security and governance to protect user funds without disrupting service.
Sources
- Cryptoslate — Summary of Google Quantum AI paper and blockchain implications: https://cryptoslate.com/why-didnt-googles-new-quantum-research-focus-on-banking-or-nuclear-codes-instead-of-bitcoin/
- Coinpaper — Coverage warning the quantum threat to Bitcoin may arrive sooner than expected: https://coinpaper.com/15907/google-quantum-threat-to-bitcoin-may-arrive-sooner-than-expected?utm_source=snapi
- U.Today — Report on Cardano being named second-most quantum-ready and implications: https://u.today/cardano-named-second-most-quantum-ready-blockchain-by-google?utm_source=snapi
For further reading on migration patterns, post‑quantum standards and cryptographic agility, consult NIST resources and the growing set of protocol-level PQC proposals in major blockchain repositories.
For discussions about how this affects specific protocols, see notes on Bitcoin and Cardano, and consider how DeFi exposure changes threat prioritization for smart‑contract ecosystems like DeFi.