How Quantum Computing Threatens BTC and ETH: Timelines, Risks, and Practical Defenses
Summary
Executive snapshot: why this matters now
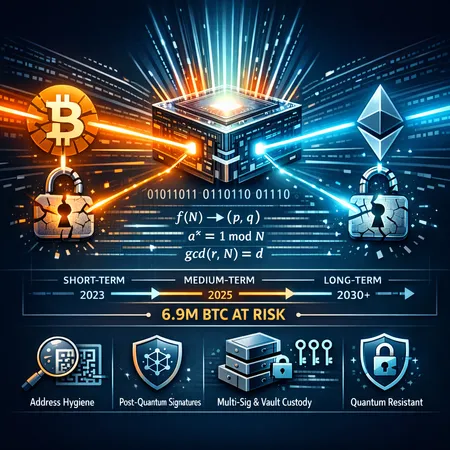
Quantum computing is moving from laboratory curiosity to an engineering arms race. For BTC and ETH — both built on elliptic-curve cryptography (secp256k1) — the relevant danger is Shor’s algorithm, which can turn public keys directly into private keys if executed on a sufficiently powerful, error-corrected quantum computer. Recent public commentary from industry figures and research groups suggests timelines may be shorter than many practitioners assumed, forcing custodians and engineers to plan actively rather than passively monitor.
This article breaks down the specific technical triggers scientists are watching, explains how coins can be stolen in practice, interprets the oft-cited “6.9M BTC at risk” figure, and delivers a prioritized, pragmatic roadmap for exchanges, custodians, and long-term holders.
What the recent analyses actually said
Justin Drake’s flag: two breakthroughs to watch
Ethereum researcher Justin Drake has framed the quantum risk in terms of two necessary engineering breakthroughs: (1) scalable, low-error quantum hardware at sufficient qubit counts; and (2) efficient, fault-tolerant implementations of Shor-style integer- and discrete-logarithm-breaking circuits. Drake’s point is not that the apocalypse is immediate, but that once both items are achieved the cryptanalytic step becomes straightforward and urgent. See his discussion summarizing how a pair of breakthroughs could compress previously optimistic timetables and enable practical attacks (analysis summarized in his commentary reported here). Read the coverage.
Google Quantum AI: the 6.9M BTC headline
Google’s Quantum AI team published an analysis estimating that roughly 6.9 million BTC (a subset of supply) could be vulnerable under a near-term quantum capability scenario. The meaning of that number is specific: it represents coins associated with addresses where public keys are already exposed or readily discoverable — the low-hanging fruit for a quantum attacker. Google’s analysis and the media amplification around it helpfully focused attention on where risk is concentrated, and also sparked sometimes-hyperbolic coverage of an imminent “end of Bitcoin.” For Google's public write-up and media summaries, see this explainer and follow-ups. Google's findings and broader reporting on industry reaction are here.
How Shor’s algorithm would be used in practice
A short technical primer
Shor’s algorithm reduces the elliptic-curve discrete logarithm problem (ECDLP) to a polynomial-time quantum computation. In simple terms: given a public key P = k*G (where k is the private key, G is the curve base point), a large enough quantum computer running Shor’s algorithm can recover k efficiently — something classical computers cannot do in feasible time for secp256k1-sized keys.
Realistic attacker workflows (attack surface)
- Public-key exposure: If an address’s public key is already known (for example, because it has been used in a spent transaction that revealed the pubkey), an attacker can target that UTXO or account immediately. This is especially relevant to some Bitcoin output types and is severe for Ethereum, where an account’s public key is effectively inferable from address usage and signature material.
- Public-key reuse: Reusing the same public key (or address types that reveal pubkeys early) concentrates risk. Reused keys are an easy priority list for attackers.
- Mid-transaction attacks (mempool race): When a user broadcasts a signed transaction, their signature and public key are in the transaction data before confirmation. A sufficiently fast attacker could, in theory, recover the private key from the broadcasted pubkey and generate a conflicting transaction (double-spend) that pays themselves, racing it to miners. In practice this requires both very fast key-recovery and network attack capability; but the possibility exists and is why broadcast-time exposure is non-trivial.
- Cold-storage exfiltration: If an attacker can recover private keys for addresses in cold storage whose public keys were previously exposed, those funds can be drained once the attacker transfers them to hot wallets.
Why ETH and BTC differ
Ethereum account addresses are directly derived in a way that makes public-key recovery easier once signatures have been observed; many ETH addresses end up with observable public key material after interactions. Bitcoin UTXO models can hide pubkeys until spend, but certain scripts (e.g., older P2PK outputs or reused keys) already expose them. That asymmetry explains why analysts worry ETH may present a larger immediate surface, while BTC still has a meaningful set of exposed coins captured in the 6.9M estimate.
Timelines: what researchers and firms are suggesting
- Justin Drake’s framing warns that two key breakthroughs could make the window narrow enough that migration must start well ahead of a fully fault-tolerant quantum computer. He highlights a plausible “by 2030–2035” range under accelerated progress assumptions, with outlier scenarios earlier if engineering surprises occur. (See the linked analysis above.)
- Google Quantum AI’s write-up highlights that, under their modeling of qubit counts and error rates, a large subset of BTC could be vulnerable sooner than some expect; the coverage includes shorter possible timelines, and the 6.9M figure is intended to spur urgent mitigations.
Important nuance: there is no consensus “drop-dead” date when every BTC and ETH becomes unsafe. Rather, risk increases as hardware capability and quantum error correction improve, and the practical attack window depends on how many keys are exposed and how fast an attacker can turn quantum cycles into private keys.
Interpreting “6.9M BTC at risk” in practice
That headline number does not mean 6.9M BTC will be stolen tomorrow. It means approximately 6.9M coins are associated with addresses where public-key data is already or easily available. Operationally this implies:
- Prioritization: custodians should treat the highest-value UTXOs with exposed pubkeys as top remediation targets. Moving a small number of addresses could dramatically reduce exposure.
- Attack efficiency: attackers will go after the easiest targets first — published pubkeys, key reuse, and large holdings in a small set of addresses.
- Temporal urgency: because these coins are already exposed, defenders don’t have the luxury of waiting for a network-level PQ migration; mitigation must be operational.
Short-, medium-, and long-term mitigation strategies
Below is a prioritized roadmap that balances feasibility with security impact.
Short term (weeks–months): operational hygiene and triage
- Inventory and prioritize: create a canonical list of addresses with revealed public keys and map balances. Start with highest-value UTXOs/accounts.
- Move exposed funds: for custodial hot and cold wallets with exposed pubkeys, migrate funds immediately to fresh addresses that have never revealed public keys. For BTC this means moving from P2PK or reused-public-key outputs to fresh P2PKH/P2SH (or newer) addresses. For ETH, treat any on-chain reused accounts as high risk.
- Stop reusing keys: enforce single-use address policy for outgoing payments; block or flag reused addresses.
- Shorten broadcast exposure windows: where possible, reduce mempool exposure by using techniques like fee bumping and careful batching, but do not rely on these as a full defense.
- Immediate policy changes: require multi-factor approval and manual review for sweeps of large, previously-exposed balances.
Medium term (6–24 months): hybrid deployments and custody layering
- Hybrid signatures: adopt hybrid transaction schemes where a classical ECDSA/Schnorr signature is paired with a post-quantum signature (both must validate). Hybrid schemes protect funds even if one primitive is broken during migration.
- Threshold/MPC upgrades: expand multi-party computation (MPC) and threshold-signature usage so single-key compromise is less useful. MPC providers can design key shares using different cryptographic families for diversity.
- Wallet and API updates: update signing stacks to include post-quantum signature libraries (e.g., NIST-aligned candidates like CRYSTALS-Dilithium for signatures and CRYSTALS-Kyber for KEM). Offer fallbacks and interoperability layers for mixed deployments.
- Custodial architecture: split critical custody into layers — an offline vault holding the last-resort keys (moved rarely, with heavy ceremony), a hot wallet for day-to-day with hybrid protection, and a quarantine process for large migrations.
Long term (1–5+ years): protocol changes and standards
- Protocol-level migration: protocol upgrades must standardize post-quantum transaction formats. For Bitcoin and Ethereum this means new transaction types and consensus checks to validate PQ signatures or hybrid constructions. Engagement with BIPs/EIPs and testnets is required now to avoid rushed forks later.
- Standardization and audits: follow NIST and other standard bodies as they finalize PQ algorithms; audit implementations aggressively and plan for algorithm agility (ability to switch algorithms without disruptive forks).
- Education and industry coordination: coordinate through industry groups, exchanges, and regulators to align migrations and avoid fragmentation that attackers can exploit.
Custody-specific technical patterns to adopt now
- Key rotation and split custody: rotate keys proactively and use time-locked withdrawal mechanisms to create windows for emergency intervention.
- Watch-only and sweeping strategies: prepare secure sweeping protocols for emergency bulk migrations of exposed balances with cold-signing workflows.
- Hybrid multisig scripts: for UTXO chains, design script templates that accept both ECC and PQ signatures (logical AND/OR where appropriate) during a transition period.
- Add quantum-risk metadata: maintain per-address metadata identifying whether a pubkey is revealed, last-used timestamp, and migration priority.
Regulatory and market implications if timelines compress
- Accelerated regulation: regulators may require custodians to demonstrate quantum-mitigation playbooks, audits, and insured migration plans. Expect mandatory incident disclosure rules to adapt to quantum-specific theft vectors.
- Insurance and liability shifts: insurers will reprice policies or require PQ-hardening for coverage. Custodians failing to address quantum risk could face denial of claims.
- Market reactions: sharp timelines or surprising breakthroughs could trigger dramatic re-pricing of crypto assets, especially for assets with many exposed public keys. Markets hate uncertainty; clear, coordinated migration communications will reduce panic.
Practical checklist: immediate actions for different actors
For exchanges and large custodians
- Run a complete address exposure audit and prioritize the top 1% of balances for immediate migration.
- Deploy hybrid-signature support in custody hot paths and integrate PQ primitives into offline cold-signing devices.
- Strengthen withdrawal controls: multi-sig/MPC thresholds, time locks, and manual approvals for large sweeps.
- Work with insurers and legal counsel to update policies and communicate plans to customers.
For smaller custodians and non-custodial wallet providers
- Enforce address single-use and educate users about key reuse risks.
- Integrate post-quantum libraries into wallets and offer migration tools for users to sweep funds into PQ-ready addresses.
- Prepare simple hybrid offerings (e.g., spend authorization requiring both classical and PQ proof).
For long-term holders and investors
- Avoid reusing addresses. Do not show off addresses that have high balances and a revealed public key.
- If you hold large balances in addresses that have revealed pubkeys, plan and execute a careful migration involving multisig custody and cold-signing ceremonies.
- Monitor credible quantum-progress reporting and custodial advisories. Tools embedded into platforms like Bitlet.app should one day provide exposure scoring — but do your own inventory now.
Monitoring signals and decision triggers
Maintain a small watchlist of technical signals that should accelerate migration steps:
- Demonstrated execution of large-scale, error-corrected quantum circuits relevant to factoring or discrete logs.
- Public releases of fault-tolerant qubit counts and error-rate reductions that match the thresholds used in models like Google’s.
- Open-source Shor implementations showing sub-hour run times at projected hardware scales.
If two or more of these signals appear, move from medium-term to emergency migration posture.
Closing thoughts
The quantum threat to BTC and ETH is not a binary “safe/compromised” flip; it’s a rising risk that can be substantially mitigated if the community acts deliberately and early. Address hygiene and custodial best practices buy time. Hybrid cryptography, MPC, and protocol upgrades are the durable fixes — but they require engineering, standards work, and coordination. Follow the science, keep migration playbooks ready, and treat the Google and Drake analyses as a clear call to action rather than a reason to panic.
Sources
- Justin Drake analysis and discussion: https://coinpedia.org/news/can-quantum-computers-break-bitcoin-by-2032-an-ethereum-researcher-thinks-it-is-possible/
- Google Quantum AI findings: https://coinpedia.org/news/google-quantum-computing-warns-6-9-million-bitcoin-could-be-at-risk/
- Industry coverage on amplification and context: https://www.newsbtc.com/breaking-news-ticker/google-end-for-bitcoin-near-quantum-computers-attack-soon/
For many engineers and custodians the first practical step is immediate inventory and migration of exposed addresses — and then an architecture review for hybrid and MPC defenses. For protocol teams, the time to prototype and standardize is now; for investors, the time to understand exposure and custody posture is also now. Keep watching both the research literature and credible industry reports, and prioritize action over speculation.
For context on how Bitcoin and Ethereum transaction models expose keys differently, and for implementation-level checklists tailored to exchange operators, contact your crypto security team or consult the growing PQ migration guides being published by custody vendors.