The New Playbook for DeFi Incident Response — Lessons from the Drift Exploit
Summary
Why the Drift exploit matters for DeFi incident response
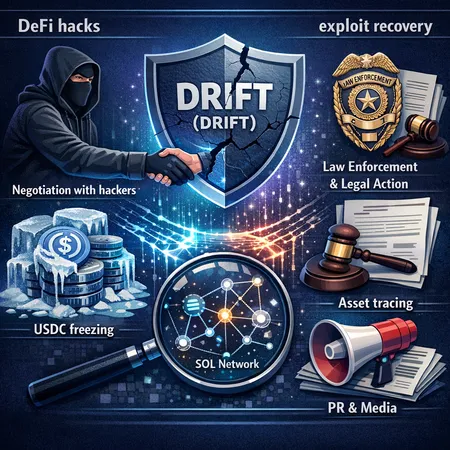
When a Solana-based protocol like Drift (DRIFT) suffers a large-scale exploit, the event becomes a stress test not just for the code but for the broader DeFi incident ecosystem: forensic tracing teams, stablecoin issuers, law enforcement, and the protocol’s own legal and communications apparatus. The recent reports that Drift engaged in settlement talks with alleged DPRK-linked attackers after a reported $285M exploit reframed what “recovery” can look like in 2024 — and forced a re-evaluation of old assumptions about frozen vs unfrozen assets and the limits of on-chain remedies.
DeFi hacks and exploit recovery are no longer purely technical problems. They’re legal, regulatory, reputational and geopolitical. Protocol teams need a playbook that treats each of those dimensions as core to effective incident response.
A quick timeline and the core facts
- A major exploit hit a Solana-based DEX, with large sums of USDC and SOL moving rapidly through mixers and bridges. The incident attracted attention because it was large, fast, and allegedly linked to actors with DPRK ties. For reporting on settlement talks, see the Drift case coverage in TokenPost.
- As funds moved on-chain, the question became: can funds be frozen, traced, or recovered — and who decides that? Circle’s public stance and the broader debate about freezing are central to this story.
- Independent researchers and on-chain sleuths (including high-profile claims documented by crypto journalists) raised questions about whether freezing mechanisms were used or could have been used in specific transfers.
Those three threads — negotiation with attackers, stablecoin freezing policy, and forensic/law enforcement options — define the modern incident-response debate.
Negotiation with attackers: pragmatic recovery or dangerous precedent?
Negotiation has gone from unthinkable to pragmatic in some DeFi circles. The Drift team reportedly entered settlement talks with alleged DPRK-linked hackers, illustrating a difficult calculus: a negotiated return of assets can be fast and materially recover value, but it brings complex trade-offs.
Benefits of negotiation
- Speed: Negotiations often yield quicker returns than on-chain tracing plus legal processes. Time matters when assets are routed through fast mixers and cross-chain bridges.
- Recoveries that wouldn’t otherwise be possible: In some cases, attackers control private keys and can reverse or repatriate funds if persuaded.
- Reduced litigation costs and fewer operational disruptions for the protocol.
Risks and downsides
- Moral hazard: Paying a ransom or settling can encourage more attacks against poorly defended protocols.
- Sanctions and legal exposure: If attackers are linked to sanctioned entities (e.g., DPRK), negotiating or paying could violate sanctions regimes or anti-money-laundering laws.
- Reputational harm: Users and counterparties may see negotiation as capitulation, eroding trust.
Negotiation is not a single tactic but a process requiring legal sign-offs, risk assessments, and strict controls. As the Drift situation shows, teams that consider this route must involve counsel and compliance experts early.
Why Circle sometimes refuses to freeze USDC — and what that means
Circle’s role as the issuer of USDC makes it a pivotal actor in exploit responses. But freezing is not a panacea and Circle has publicly explained reasons for refusal in some cases. A detailed analysis of their rationale can be found at Blockonomi, which explains the trade-offs Circle weighs before acting.
Key rationales behind refusals
- High false-positive risk: Automatic freezing risks trapping legitimate users’ funds when heuristics misidentify activity.
- Legal and procedural constraints: Freezing requires a legal basis, clear ownership proofs, or a court/authority directive; doing so impulsively can expose Circle to legal challenge.
- Systemic risk considerations: Broad or aggressive freezing could undermine the fungibility and reliability of USDC as a market-grade stablecoin.
There is also public pushback from investigators and sleuths. For example, reporting summarized by crypto.news highlights allegations and debate around whether Circle failed to halt suspicious USDC flows in a broader set of incidents — an argument that has reputational and compliance implications for the issuer.
Practical takeaway: protocol teams cannot rely on a blanket expectation that a stablecoin issuer will freeze funds. That uncertainty must be accounted for in any response playbook.
Forensic tracing and law enforcement: powerful but imperfect
On-chain tracing firms and law enforcement are essential partners after a major exploit. Forensic tracing can follow the money, identify counterparty addresses, and sometimes link activity to known cluster labels. But there are clear limitations:
- Speed: Chain analysis takes time. Mixers, privacy layers, cross-chain bridges and rapid token swaps can outpace tracing efforts.
- Jurisdictional limits: Even if a tracer identifies a cluster, law enforcement needs jurisdictional authority and cooperation to seize or compel action.
- Traceability vs. recoverability: Tracing identifies where the money went; it does not automatically recover it. Seizure or freezing often requires centralized actors or court orders.
A realistic playbook treats forensic teams and law enforcement as necessary but not sufficient — they are one leg of a recovery stool.
Comparing negotiation, tracing, and legal routes: a decision framework
When an exploit happens, teams typically face three broad options: negotiate, pursue forensic/law enforcement recovery, or attempt technical mitigation (e.g., pausing contracts, clawbacks where feasible). Each path has strengths and limits.
- Negotiate when: the attacker is reachable, a credible channel exists, funds can be committed conditionally, and legal counsel affirms compliance with sanctions and AML rules.
- Rely on tracing & law enforcement when: the attacker is anonymous or linked to criminal networks, the jurisdictional environment is favorable, and seizing or freezing via courts or custodians is realistic.
- Prioritize technical mitigation when: protocol controls (timelocks, multisigs, emergency pause) can blunt further losses and preserve user safety.
Often the optimal strategy is a hybrid: immediately enact technical containment, start forensic tracing, notify law enforcement, and open a controlled negotiation channel if legal counsel advises it’s defensible.
The limits of on-chain recovery: what smart contracts can’t fix
Smart contracts are immutable by design. Even with upgradable modules or admin keys, many protocols lack the unilateral ability to claw back assets without creating centralization risks. On-chain recovery faces obstacles:
- Cross-chain obfuscation: Funds split across chains and bridges are harder to recover.
- Privacy tools and mixers: Tumblers and privacy-preserving chains make attribution slow and messy.
- Liquidity and slippage: Liquidating or reclaiming large troves of tokens can crash markets and reduce effective recovery value.
Protocols should plan for the reality that some or most stolen assets may be unrecoverable on-chain — which is why pre-incident planning matters.
Building a practical incident-response playbook (legal, technical, and PR)
Below is a consolidated framework protocol teams can adapt. Each item should be codified, rehearsed, and assigned to named owners.
1) Pre-incident: governance & contracts
- Emergency keys and governance thresholds: Define multisig quorum, emergency pause abilities, and responsible disclosure policies.
- Treasury diversification & circuit breakers: Keep operational funds segmented and include timelocks or recovery windows.
- Insurance and custodial relationships: Pre-negotiate coverage and T&Cs with insurers and custodians.
2) Triage: immediate post-exploit steps (first 0–24 hours)
- Technical containment: Pause contracts, disable key integrations, and freeze on-chain actions where governance permits.
- Evidence preservation: Snapshot logs, contract state, and transaction traces. Preserve multisig approval ballots and signer metadata.
- Activate incident response team: Security engineers, legal counsel, compliance officer, PR, and senior governance representatives.
3) Forensic & legal engagement (24–72 hours)
- Hire an on-chain forensics firm and share access to logs; begin tracing funds and mapping clusters.
- Brief external counsel on sanctions and money-transmission risks; run sanctions-screening on recipient clusters.
- Notify relevant law enforcement and regulators where applicable; have an evidence package ready.
4) Negotiation protocol (if considered)
- Legal pre-check: Confirm negotiating or transferring value back will not breach sanctions, AML, or export controls. If DPRK ties are plausible, do not negotiate without specialized sanctions counsel.
- Negotiation governance: Require a governance vote or an emergency council that includes legal and compliance signoff. Limit authority and set clear recovery KPIs and escrow mechanics.
- Use intermediaries and escrow: Where possible, use vetted intermediaries, cryptographic escrow, or conditioned fund returns rather than direct payments.
5) PR and community communications
- Single source of truth: Appoint a spokesperson and a cadence for updates (hourly in first 24 hours, then daily). Avoid speculation while being transparent about known facts.
- Templates and transparency: Prepare templated messages for Discord, Twitter, forums and the protocol blog; explain technical steps and mitigation while avoiding tactical detail that could aid attackers.
- Post-incident report: Publish a detailed incident report with timeline, actions taken, and lessons learned. This is crucial for market trust and future audits.
6) Post-recovery: governance, audit, and insurance reconciliations
- External audit: Commission a third-party security review and patch vulnerabilities.
- Treasury replenishment: Communicate how losses will be covered (insurance, protocol reserves, community solutions, or retroactive funding).
- Policy updates: Update the incident-response plan, playbooks, and run tabletop exercises.
Practical checklists and partners
- Forensics partners: Pre-vet 2–3 firms and keep retainer agreements available.
- Legal partners: Engage counsel familiar with sanctions, OFAC, and crypto AML rules.
- PR firm: Have a crisis comms partner on call.
- Negotiation intermediaries: Identify firms experienced with hostage-recovery-style negotiation in crypto (with strong compliance controls).
Remember: protocol teams should not assume Circle or other stablecoin issuers will freeze funds automatically. Build playbooks that do not rely on a single upstream actor.
Governance and moral hazard — balancing incentives
Protocols must also consider long-run incentives. If negotiating becomes the de facto response to large exploits, attackers may target weaker projects expecting a payday. To mitigate this:
- Publish clear policy thresholds: Under what conditions the protocol would consider negotiation, and what governance approvals are required.
- Use conditional recoveries: Structure deals so attackers must demonstrate knowledge of private keys or provide verifiable returns before receiving any payment.
- Strengthen defensive posture: Increase bug bounties, invest in audits and runtime monitoring, and require better treasury hygiene across the ecosystem.
Conclusion: a hybrid, legally-informed approach is now essential
The Drift case exposed a new normal: funds can move off-chain and across jurisdictions faster than legal processes can react, and issuer freezes are not guaranteed. A modern incident-response playbook must be hybrid — combining rapid technical containment, professional forensic tracing, clear legal sign-off on any negotiation, and disciplined communications.
For DeFi teams, security leads and counsel, that means rehearsing scenarios, pre-negotiating relationships with forensic firms and legal teams, and codifying rules for when negotiation is permissible. The goal is simple: minimize loss and systemic harm while staying within the law and protecting long-term reputation. Services across the ecosystem — from on-chain tracing and custodians to platforms such as Bitlet.app that integrate custody and reconciliation workflows — will be part of that architecture, but they are only one part.