Vitalik's Four-Point Quantum Security Roadmap for Ethereum — A Practical Guide

Summary
Executive summary
Vitalik Buterin’s four-point quantum security roadmap is an early-but-essential blueprint: it prioritizes research, enshrines hybrid cryptography while migration tech matures, proposes explicit migration planning, and insists on better ways to measure and communicate quantum risk. Read together with the Ethereum Foundation’s Strawmap (the multi-year upgrade blueprint), this amounts to a program-level security project — not a single EIP — that protocol engineers and product managers must institutionalize now.
For a quick read of Vitalik’s outline see coverage of his proposed plan here and here.
Why quantum resistance is a practical concern today
Quantum computers that break deployed public-key algorithms are not guaranteed next month — but the risk horizon is shortening. Progress on superconducting qubits, error correction experiments, and national-level investments mean that the cryptographic community treats quantum risk as an engineering problem with a multi-year migration window, not an academic fantasy.
That matters for blockchains because many blockchain systems, including Ethereum, bundle long-lived signatures and public keys into immutable state. Keys used today to control funds or mint assets may be targeted years from now if past signatures or public keys are exposed. In short: the long-lived nature of on-chain state magnifies even moderately probable future risks.
While Bitcoin often dominates headlines, the practical implications in smart-contract ecosystems and DeFi — where state and proofs are reused across chains and layers — make quantum resistance a priority for Ethereum-first infrastructure.
The four points, explained in plain language
Vitalik’s plan can be summarized as four pragmatic pillars. Below I unpack each and translate it into concrete engineering workstreams.
1) Research priorities: sharpen the threat model and the usable toolset
Plain language: fund and coordinate research into what quantum computers will realistically break, how fast, and which cryptographic replacements are the best fit for blockchains.
Practical implications:
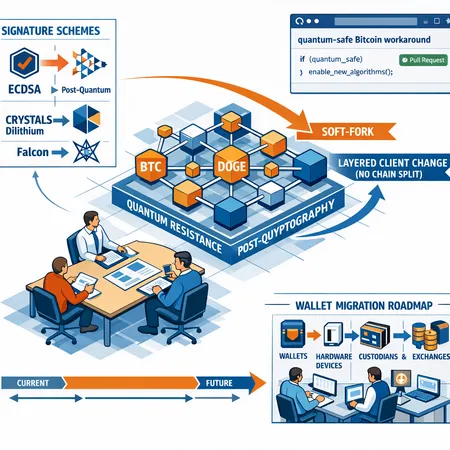
- Produce a prioritized list of candidate post-quantum signature and hashing schemes that balance security, size, and verification cost on-chain (for example, NIST-selected families like CRYSTALS-Dilithium for signatures and Kyber-like KEMs for hybrid key exchange are relevant starting points).
- Benchmark post-quantum verification costs across EVM and popular ops (signature verification, aggregation, batch verification).
- Research zk-friendly post-quantum primitives — needed for efficient zero-knowledge proofs.
This is research infrastructure as much as crypto math: test vectors, deterministic benchmarks, and reference implementations that clients and wallet vendors can adopt.
2) Hybrid cryptography: pragmatic transition via combined schemes
Plain language: don’t rip out current crypto overnight. Use hybrid signatures that pair today’s algorithms (ECDSA, BLS where used) with a post-quantum companion so that an attacker needs both classical and quantum breakthroughs.
Practical implications:
- Define canonical hybrid signature formats and wire encodings that client software (wallets, validators) can parse.
- Standardize how to store hybrid keys in user wallets and smart-contract accounts; decide how and when verification fails over (e.g., require both parts, accept either, or prioritize post-quantum portion).
- Plan the UX for private key backup and rotation — larger key material and different math families change UX constraints.
Hybrid approaches lower immediate risk while giving time to optimize pure post-quantum schemes and minimize large-scale state migrations.
3) Migration plans: how to move billions of addresses and contracts safely
Plain language: create migration strategies and tooling that let wallets, smart contracts, rollups, and validators adopt new primitives without catastrophic chain splits.
Migration levers:
- Soft-fork friendly upgrades that introduce new verification opcodes or precompiles while leaving old semantics intact.
- Contract-level adapter libraries: standardized contract modules that implement hybrid verification so project code can migrate incrementally.
- On-chain key-rotation tooling and multisig/recovery patterns that let custodians rekey in bulk.
This pillar requires operational playbooks for validators (client update cadence), exchanges (cold-wallet migration), and rollups (state-migration strategies).
4) Risk measurement: translate probability into operational decisions
Plain language: create quantifiable metrics and dashboards that tell stakeholders how imminent the threat is, how much state is exposed, and how to prioritize mitigation.
Examples of useful metrics:
- Amount of ETH and tokens controlled by addresses that publish public keys on-chain.
- Number and value of smart contracts that embed or depend on vulnerable signature schemes.
- Time-to-migrate estimates for exchanges, custodians, and top DeFi protocols under normal ops.
These metrics inform governance windows, client update urgency, and resource allocation for migration incentives.
How Vitalik’s roadmap fits into the Strawmap / 2029 upgrades
The Ethereum Foundation’s Strawmap outlines seven network upgrade focal points through 2029. Quantum-resistance work is not necessarily a discrete network upgrade; it’s a cross-cutting capability that should be folded into several Strawmap workstreams: consensus-layer robustness, execution-layer precompiles, account abstraction and account model changes, and zk tooling.
You can read the Strawmap blueprint here.
Concrete interactions:
- Some Strawmap upgrades are natural windows to introduce new precompiles (e.g., a future execution-level upgrade can add a verification precompile for a post-quantum signature).
- Other upgrades that change account models or introduce additional opcodes can be leveraged to add hybrid key formats and storage slots for migration metadata.
Treat Strawmap upgrade windows as opportunities to stage and coordinate migration — each upgrade is a schedule anchor for validators, client teams, and app developers.
Technical pain points and likely contention areas
Below are the main engineering challenges you should expect and plan around.
Poseidon precompile and zk proofs
Poseidon is a family of zk-friendly hash functions used widely in zk circuits because they are much cheaper inside proofs than generic hashes. Several zk stacks — including zkEVM workstreams — expect efficient Poseidon support to keep proof costs low. However, developer discussion has flagged a missing Poseidon precompile in some zkEVM stacks, which would force awkward workarounds and higher gas/proof costs.
Read a developer critique about the missing Poseidon precompile here.
Implications:
- Without a standardized Poseidon precompile, rollup and prover implementations duplicate logic, or prove using more expensive primitives. That increases costs for L2s and complicates any migration to quantum-resistant hashes that also need to be zk-friendly.
- Adding a precompile requires EIP design, client changes, and a coordinated activation strategy that avoids breaking existing rollups.
Backward compatibility and account/address models
Adding new signature schemes or hybrid formats is easy in theory but messy in practice: addresses, contract verification logic, storage layout, and tooling all assume a canonical key/signature shape.
Choices that teams face:
- New account types vs. in-place extension of existing accounts. New account types simplify migration but fragment the address space. In-place extensions preserve addresses but require complex parsing logic.
- Who pays gas for migration? If contracts are required to run on-chain rekeying steps, costs fall on users or projects.
ZK proofs and post-quantum primitives
Many post-quantum primitives are less friendly to aggregation or succinct on-chain verification. That directly affects rollups and zkEVM designs, which rely on small proof sizes and efficient verifier circuits. Therefore, workstreams should prioritize zk-friendly post-quantum schemes or hybrid approaches that keep verifier costs low.
Governance and rollout challenges
Quantum-resistance is not only technical; it’s a governance program:
- EIP standardization: crafting EIPs that describe hybrid formats, precompiles, and account changes will require cross-client sign-off and spec clarity.
- Upgrade cadence: validators and staking providers need clear timelines and long lead times for client updates. The social coordination cost is non-trivial.
- Contention risk: if some clients or major validators refuse upgrades, the migration could be contentious. The roadmap must build consensus through specification work, testnets, and widely adopted reference implementations.
Practical checklist: what wallets, validators, and projects should do now
Below are pragmatic, prioritized actions your team can present to stakeholders.
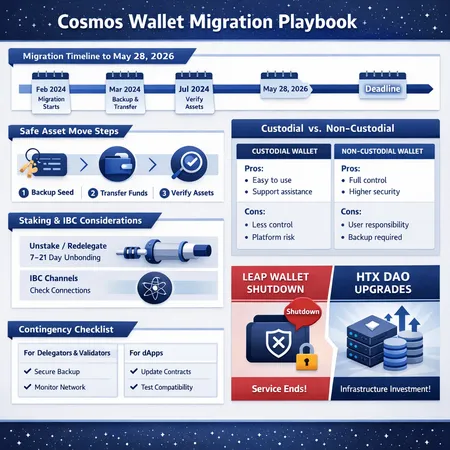
For Wallets and Custodians:
- Begin audits of key storage formats and wallet SDKs for post-quantum compatibility. Plan for larger key sizes and changed serialization.
- Implement support for hybrid signatures in hot-wallet libraries and offer a key-rotation UX for custodial users.
- Coordinate with exchange partners and custodial clients to schedule staged migrations and bulk key rotations.
For Validator Operators and Client Teams:
- Add post-quantum test cases to client test suites and maintain experimental branches that support new precompiles and opcodes.
- Engage in testnets that prototype staged upgrades and exercise mass key-rotation scenarios.
- Prepare operator playbooks for upgrade windows with rollback and emergency-response policies.
For Protocol Engineers and Smart-Contract Teams:
- Identify critical contracts that expose public keys or rely on signature schemes; instrument these with monitoring that measures exposed value.
- Adopt adapter libraries so that contract-level verification can switch to hybrid verification without changing business logic.
- For zk projects and zkEVM teams, lobby and prepare for Poseidon precompile or equivalents; measure proof costs with PQ primitives and plan for optimizations.
For L2s and Rollup Operators:
- Build mapping strategies for migrating rollup state (e.g., rekeying accounts, updating fraud-proof/verifier logic) and test them in private testnets.
- Coordinate with mainnet client teams to ensure verifier precompiles are available or that gas costs for new verifiers are understood.
A note for product managers: all of the above need budgets, testnet cycles, and migration incentives. Start conversations with legal/compliance and custodian partners now.
Timeline expectations and implications for ETH staking and L2s
Timeline: expect a multi-year program. The Strawmap’s upgrade cadence through 2029 provides practical anchor points where precompiles, account-model changes, and consensus tweaks can land. Vitalik’s proposal nudges teams to treat quantum resistance as parallel work that must converge with those upgrade windows.
Implications for ETH staking and validators:
- Validators must be prepared for software updates that introduce new verification primitives or change slashing-related logic. Coordinated client releases and long activation delays (several months) are likely.
- Stakers should not panic. A careful migration with client coordination can avoid forced mass exits. However, validator operators must test upgrades rigorously and understand upgrade activation conditions.
Implications for L2s and zkEVMs:
- L2s have a critical dependency on verifier efficiency. If post-quantum verifier costs increase drastically, rollups may face higher prover gas and user fees unless mitigations (Poseidon-like zk-friendly PQ primitives or precompiles) are introduced.
- zkEVM teams should prioritize adding Poseidon precompile support where it reduces proof costs and helps integrate PQ primitives into circuits.
Recommended near-term roadmap for teams (90–540 days)
0–3 months
- Inventory: measure exposed value (addresses, contracts) and publish a migration-risk dashboard.
- Prototype hybrid signatures in internal builds and wallets.
3–12 months
- Deploy testnets with candidate precompiles (e.g., Poseidon and PQ verifier stubs).
- Publish EIP drafts for hybrid formats and precompile interfaces; gather client feedback.
12–18 months
- Run coordinated testnet activations simulating mass key rotations and validator upgrades.
- Start incentivized migrations for high-value custodians and exchanges.
18–36 months
- Target mainnet activation windows aligned with Strawmap upgrades. Continue metric-driven rollout and monitoring.
This timeline assumes steady progress in PQ crypto standardization and no sudden breakthroughs that compress the window.
How to communicate risk to stakeholders
Translate technical progress into three stakeholder-focused artifacts:
- A quantified dashboard (exposed value, migration progress, expected exposure after each upgrade).
- A migration playbook that lists who needs to act and when (wallets, validators, exchanges, major dApp teams).
- A governance timeline with proposed EIP milestones and release windows aligned to Strawmap anchors.
These artifacts let Ops, Legal, and Finance make budgeting and contractual decisions rather than treating the topic as theoretical.
Conclusion: treat this like software lifecycle management
Vitalik’s four pillars move quantum resistance into program management territory: research, hybrid mitigation, migration playbooks, and risk measurement. The engineering tasks are concrete — precompiles, EIPs, hybrid signature formats, testnets — but they require governance, coordination, and funding.
Protocol teams should align quantum-resistance work with the Strawmap upgrade windows, advocate for missing pieces like a Poseidon precompile where appropriate, and build migration-first tooling now. Bitlet.app and other infrastructure providers that manage keys and custody should be part of these conversations because their customers will expect clear migration offers and timelines.
If you are a protocol engineer or product manager: draft the migration dashboard and an EIP outline this quarter. Fund the benchmarks that show verifier cost for candidate PQ schemes. Use the Strawmap upgrade anchors to make the project visible and schedulable.
Sources
- Vitalik’s four-point quantum security proposal and roadmap overview: https://thenewscrypto.com/vitalik-buterin-unveils-four-point-quantum-security-plan-for-ethereum/?utm_source=snapi
- Additional coverage of Vitalik’s quantum resistance roadmap: https://crypto.news/vitalik-buterin-to-make-ethereum-quantum-resistant/
- Ethereum Foundation Strawmap blueprint (seven network upgrades until 2029): https://blockonomi.com/ethereum-foundation-releases-strawmap-blueprint-seven-network-upgrades-until-2029/
- Developer criticism about the missing Poseidon precompile and zkEVM privacy push: https://u.today/ethereum-missing-key-element-poseidon-hash-in-zkevm-privacy-push-developer-claims?utm_source=snapi