Solana Security After Drift: STRIDE, Protocol Risks, and Near-Term Price Implications
Summary
Executive overview
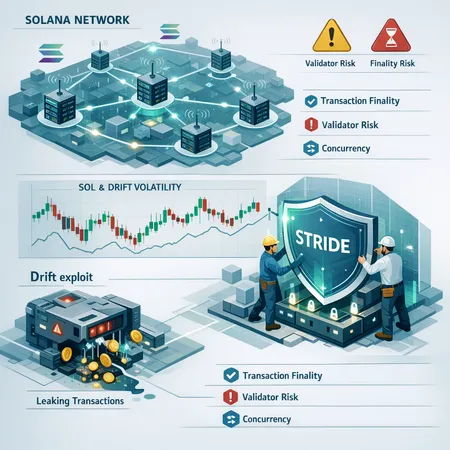
High-profile incidents like the DRIFT exploit re-centered attention on the Solana stack: where protocol design, program-level access controls, and ecosystem practices meet. The $280 million-class exploit didn’t just drain a single protocol — it revealed weak links in how Solana programs compose and how quickly state changes propagate across a high-throughput network. For many teams and traders, that means reassessing transaction finality, validator risk, and the operational hygiene of DeFi contracts built on Solana.
For background on the ecosystem response, the Solana Foundation recently launched the STRIDE ecosystem security programme to coordinate audits, bug bounties, and secure development practices across projects (announcement). Coverage of the post-exploit security push and the context of the Drift incident is available in industry reporting (AmbCrypto overview).
This article examines: (1) what the Drift exploit exposed; (2) what STRIDE can and cannot do; (3) Solana-specific on-chain and protocol risks — especially concurrency and finality characteristics; (4) how security developments map to near-term SOL price and sentiment; and (5) recommended operational steps for projects and users.
What the DRIFT exploit exposed
The DRIFT exploit was not a one-off logic bug in isolation; it functioned as a stress test of composability and privilege assumptions across a live DeFi stack. Attackers were able to leverage program interactions and oracle manipulations to create inconsistent views of state across transactions, amplifying losses rapidly.
Two core lessons stand out:
- Privilege and access assumptions were violated. Several programs relied on implicit trust or broad approvals between contracts. When one component behaved unexpectedly, upstream and downstream programs had no adequate guards.
- Speed exacerbated contagion. Solana’s high throughput and low-latency execution enable rapid liquidation cascades. That property is a strength for UX, but a risk when combined with insufficient on-chain circuit breakers.
The exploit’s fallout prompted a broad security push. Industry coverage framed the initiative as both reactive and systemic — an attempt to close gaps revealed by the breach while hardening the DeFi layer overall (AmbCrypto analysis).
Solana Foundation’s STRIDE programme: scope and realistic expectations
STRIDE is a visible, centralized effort to coordinate security improvements across the Solana ecosystem. Its pillars include funded audits, bounty expansion, developer tooling, and shared best practices. The announcement positions STRIDE as a long-term program to uplift the maturity of Solana projects (Solana Foundation statement).
What STRIDE can realistically do:
- Standardize basic hardening measures (e.g., canonical ACL patterns, safer cross-program invocation templates, and recommended oracle integrations).
- Subsidize audits and higher bounties, which will attract more rigorous third-party review of critical code paths.
- Fund tooling that surfaces risky permission graphs, enabling teams to spot broad approvals and single points of failure earlier in CI.
What STRIDE will not immediately solve:
- Protocol-level design trade-offs. STRIDE can promote best practices at the program level, but it cannot (and does not purport to) change core execution semantics like concurrency models or the practical limits of validator finality.
- Human operational errors and coordination failures across independent projects. Many vulnerabilities arise from gluing independent contracts together — an area where incentives and governance structures matter as much as tooling.
In short: STRIDE raises the ecosystem’s baseline security posture, but it’s mitigation rather than cure.
On-chain and protocol risks unique to Solana
Solana’s architecture diverges from EVM chains in ways that matter for security and risk modelling. Two categories are especially relevant for DeFi teams and traders: concurrency characteristics and validator-driven finality behavior.
Concurrency and state consistency
Solana achieves high throughput with a parallelized runtime. Programs can often process many transactions simultaneously, but concurrency requires careful state access patterns. If programs assume serialized updates or rely on ephemeral invariants, concurrent execution can lead to race conditions and inconsistent state views. Attackers can exploit these windows to execute sandwich-like strategies or to cause logic to evaluate with stale or partial data.
Design implications:
- Favor explicit locking or versioning on shared state slots where invariants are critical (e.g., margin calculations, collateral accounting).
- Avoid implicit cross-program assumptions about order. Where possible, use single-source-of-truth or deterministic reconciliation flows.
Transaction finality and validator behavior
Solana’s concept of finality differs operationally from probabilistic finality in some other chains. Validators and leader rotation patterns, combined with partial network partitions, can create scenarios where transactions appear finalized quickly but may be re-organized in edge cases. That practical nuance increases validator risk — the risk that a node or subset of nodes behaves in a way that changes transaction ordering or exposes frontier states.
Operational consequences:
- Fast apparent finality improves UX but shortens the window for human or automated intervention. Protocols should assume that rollbacks, while rare, are possible and plan compensating controls.
- Validator misconfiguration or centralization increases systemic risk. Projects must evaluate the decentralization and incentives of the validator set they rely on.
Other Solana-specific vectors: program upgrades, CPI complexity, and compressed data
- Program upgradeability and broad admin keys remain a common operational vector. Centralized upgrade keys without multi-sig checks create single points of failure.
- Cross-program invocations (CPIs) are powerful but multiply the attack surface: a bug in a dependency can cascade into otherwise-safe logic.
- Compact state and account-compression techniques save fees but can complicate forensic analysis after an incident.
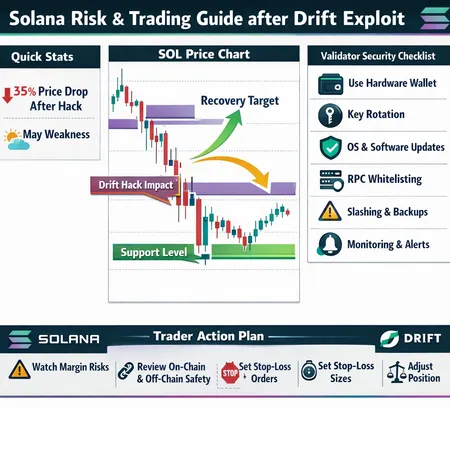
How security developments map onto near-term price action and trader sentiment
Price and security are tightly coupled on event-driven chains. The market’s short-term reaction to breaches and mitigations tends to unfold in predictable phases:
- Initial shock and flight to liquidity. Exploits like DRIFT put immediate sell pressure on both the protocol token (DRIFT) and the native chain token (SOL) as traders de-risk and margin calls cascade.
- Information-seeking and sentiment digestion. Investors look for credible remediation commitments: audits, clawbacks (rare), or coordinated stop-gap measures. Announcements like STRIDE can arrest panic if they are seen as credible and well-resourced.
- Volatility during the remediation window. Even with STRIDE, the market prices in residual uncertainty. Technical analyses during this period are often noisy: bullish patterns may form, but fundamental tail-risks remain.
Recent market commentary pointed to SOL’s retracement below $100 amid sell-offs and risk-off flows, highlighting how security headlines can amplify price moves (Bitcoinist market context). Technical analysts argue there is breakout potential but also structural risk that can cap rallies until confidence rebuilds (Coinpaper technical note).
Practical takeaways for traders:
- Treat SOL and derivative positions as event-driven trades in the near term. Position sizing should account for binary security events.
- Monitor ecosystem-level signals: major audit completions, STRIDE-funded milestones, and on-chain indicators of liquidations or large transfers.
- Use order types and layered exits: set explicit thresholds for de-risking rather than relying on instantaneous finality in a panic.
Recommended operational steps for projects and users building on Solana
Security teams and DeFi project leads should take a layered, prioritized approach. Below are practical measures ranked by impact and feasibility.
For project leads and security engineers
- Canonicalize access control patterns
- Implement least-privilege defaults. Avoid granting broad approvals to multisig or program accounts unless strictly necessary. Link compaction and ACL verification into CI.
- Add on-chain circuit breakers and staged fail-safes
- Build emergency pause functionality that can be activated by a robust governance or multisig process. Use time-locked rollbacks or pause windows to give teams breathing room after detecting anomalies.
- Harden cross-program invocations (CPIs)
- Explicitly verify caller identities and expected state shapes. Avoid implicit assumptions that a CPI caller is benign.
- Increase observability and anomaly detection
- Instrument critical flows with alerting for abnormal balance drift, oracle deltas, or unusual CPI patterns. Real-time dashboards plus automated alarms shorten detection-to-response time.
- Fund ongoing audits and red-team engagements
- Use STRIDE funding where available for deep audits, but also run regular adversarial simulations and bounty-driven tests.
- Enforce multi-stage deployments
- Canary deployments, staged migrations, and shadow testing on testnets or devnets reduce the blast radius of logic changes.
- Reassess upgradeability governance
- Replace single-admin upgrade keys with multi-sig or on-chain timelocks and transparent upgrade proposals.
For users and liquidity providers
- Be conservative with approvals. Use wallet patterns that allow granular approvals or per-contract limits.
- Diversify exposure across chains and protocols if yields are attractive but concentrated.
- Avoid providing deep liquidity to freshly deployed contracts without audited code and visible security controls.
- Follow trustworthy community channels and watch for STRIDE-backed audit announcements as a signal of lower residual risk.
How to monitor progress: metrics and signals that matter
Teams and traders should track a small set of observable signals to gauge whether Solana’s security posture is genuinely improving:
- Number and depth of STRIDE-funded audits published, and whether critical issues were fixed publicly.
- Bounty activity and average payout sizes (higher bounties correlate with better incentive alignment for white-hat research).
- On-chain metrics: frequency of unusual CPI patterns, median time-to-detection for anomalies, and concentration of program admin keys.
- Validator decentralization metrics: distribution of stake and incidence of correlated misconfigurations.
Bitlet.app users and teams can incorporate these signals into operational dashboards to manage exposure and automate conservative behaviors.
Conclusion
The DRIFT incident was a harsh reminder that high throughput and low latency come with distinct security trade-offs. STRIDE is an important ecosystem-level response — it raises the security baseline by funding audits, tooling, and best practices — but it does not eliminate the underlying protocol-level trade-offs around concurrency and practical finality. Traders should treat SOL as an event-sensitive asset until market participants see sustained, measurable improvements in audit coverage and operational practices. Project teams must harden access controls, add on-chain circuit breakers, and operationalize detection and staged deployment workflows.
Solana remains a fertile environment for innovative DeFi experiences, but those innovations must be matched with a commensurate investment in security discipline. For operators, the path forward is pragmatic: prioritize the highest-impact mitigations, use STRIDE resources where appropriate, and assume adversaries will probe any remaining gaps.
Sources
- Solana Foundation STRIDE announcement: https://cryptonews.com/news/solana-foundation-stride-ecosystem-security-program/
- AmbCrypto coverage of the security push after the Drift breach: https://ambcrypto.com/solana-rolls-out-stride-a-defi-wide-security-push-after-285-mln-drift-breach/
- Market context on Solana price retracement: https://bitcoinist.com/what-to-expect-solana-price/
- Technical analysis and structural risk note: https://coinpaper.com/16042/solana-sets-up-for-a-breakout-but-may-risk-still-hangs-over-sol?utm_source=snapi
For protocol-level background and ecosystem updates, see Solana and broader DeFi discussions.