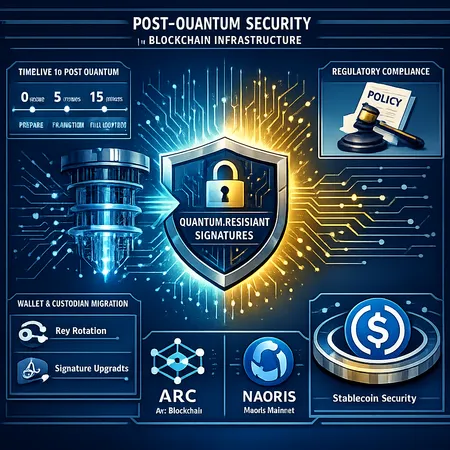
Preparing for the Quantum Era: Post-Quantum Security for Stablecoin Rails — Arc & Naoris Case Studies
Summary
Executive summary
Quantum-resistant cryptography is no longer a purely academic concern — it is becoming an operational priority for financial rails and infrastructure projects with long-lived assets. Projects like Circle’s Arc Layer‑1 (supporting USDC on ARC) and the Naoris Protocol mainnet launch are early, public examples of teams treating post‑quantum security as a design constraint rather than a vague future problem. This article explains the technical choices available, why stablecoin rails and national‑security‑sensitive projects are moving now, practical timelines for risk, migration challenges for wallets and custodians, and the likely regulatory and policy fallout.
Why quantum resistance matters now for stablecoin rails and critical infrastructure
Classical public‑key cryptography used across blockchains (ECDSA, EdDSA, RSA) relies on mathematical problems that are vulnerable — in principle — to large scale quantum computers running algorithms like Shor’s. For stablecoins and critical payment rails, the implications are acute for two reasons:
- Systemic duration of risk. Stablecoins and their settlement records are expected to persist for years or decades. An attacker who records signed transactions today can attempt to break signatures offline later — the “store now, break later” threat. This is particularly relevant to USDC as a widely used dollar rail.
- Concentration and target value. Large mint/burn keys, multisig signers held by custodians, or privileged validator keys form high‑value targets. A breakthrough that compromises a small set of keys can cascade into systemic losses.
Circle’s announcement that the Arc blockchain will include post‑quantum signature schemes for stablecoin rails is a clear signal that major infrastructure providers view this as a near‑term engineering requirement. See the Arc announcement for technical framing and intent: Circle’s Arc post‑quantum update.
Similarly, the Naoris Protocol mainnet launch explicitly positions itself against an accelerating quantum disruption timeline, showing that national‑security‑conscious projects are also building PQC into their roadmaps: Naoris Protocol mainnet goes live.
For many organizations — and for those tracking market infrastructure more broadly — this is a shift from “we will consider this later” to “we must design for this now.” For context: for many traders, Bitcoin remains the primary market bellwether, but stablecoin rails form the plumbing. Protecting that plumbing is a different class of operational priority.
Post‑quantum signature schemes: the high‑level taxonomy
Post‑quantum signatures are not a single algorithm; they are families with distinct trade‑offs. Most practical deployments will evaluate a subset of these choices:
Lattice‑based signatures
- Examples: CRYSTALS‑Dilithium (NIST‑selected).
- Pros: Reasonable performance, relatively compact keys and signatures compared to some alternatives. NIST’s selection gives confidence in standardization.
- Cons: Newer mathematics, considerations about implementation correctness and side‑channel resistance.
Hash‑based signatures
- Examples: SPHINCS+ (stateless hash‑based), XMSS, LMS (stateful).
- Pros: Strong security assumptions based only on hash functions; conservative security model.
- Cons: Often large signature sizes (SPHINCS+ improved but still larger than ECDSA) and, for stateful schemes, operational complexity.
Other families (multivariate, code‑based)
- Have niche deployments and different performance/size tradeoffs; less traction for mainstream blockchain signatures so far.
Practical hybrid approaches
Because each family has pros and cons, many teams adopt hybrid signatures (classical + PQ scheme) during a transition. Hybrid signing provides backward compatibility and defense‑in‑depth: an attacker must break both the classical and the PQ components to forge signatures.
Case study: Arc (USDC rails) — engineering and risk posture
Circle’s Arc is a practical example of a stablecoin issuer embedding PQC into the chain’s signing model. The announcement indicates a willingness to support post‑quantum signature schemes for the rails that handle USDC, prioritizing long‑term integrity of stablecoin issuance and settlement.
Key implications for custodians and issuers:
- Upgrade paths: Node software and validator stacks must accept different signature formats and validate hybrid signatures. That implies coordinated releases across validators and custodians.
- Key management: Issuers like Circle must decide whether to rotate mint/burn keys into PQ algorithms or use hybrid keys. For custodians storing keys on behalf of issuers, HSM vendors will need to support PQ algorithms and standards.
- Gas and storage costs: Larger signature sizes can increase on‑chain costs; Arc and similar Layer‑1s need to manage fees and block size implications.
Arc’s move is instructive: stablecoin issuers cannot treat cryptography as a static dependency; rails must plan upgrades that balance security, cost, and decentralization.
Case study: Naoris mainnet — national‑security framing
Naoris positions itself with an explicit focus on quantum resilience as an operational differentiator. For projects linked to national security, defense data, or sovereign financial infrastructure, the tolerance for theoretical cryptographic risk is much lower. A few takeaways from Naoris’ launch:
- Threat model tightness: Projects with national‑security awareness factor in adversaries with substantial resources and long time horizons. That pushes them to adopt conservative PQC choices and redundancy.
- Interoperability concerns: When a sovereign or government agency requires PQC, cross‑chain communications and bridging must also be PQ‑aware to avoid weak links.
Naoris’ timing echoes a broader industry trend: when the expected cost of migration is small relative to potential future systemic losses, actors move sooner.
Practical timelines and risk modeling
How urgent is the threat? Honest risk modeling uses multiple inputs:
- Quantum hardware progress. Estimates vary: some experts place practical, large‑scale quantum computers capable of breaking ECDSA in a decade or more; others warn of faster progress. High‑value actors behave as if the timeline could accelerate. The Naoris announcement explicitly treats the timeline as accelerating.
- ‘Harvest now, decrypt/break later’. Because attackers can store ciphertexts and signatures today, any asset with long confidentiality or integrity requirements is at risk even if the quantum break is years away.
A pragmatic operational split:
- Near term (0–3 years): Inventory keys, adopt PQC in new deployments, test hybrid signatures in devnets.
- Medium term (3–7 years): Begin wide operational rollout for critical keys (master signing keys, custodial multisigs) using hybrid or full PQ keys; hardware and HSM vendors certified for PQC.
- Long term (7+ years): Full deprecation of vulnerable classical keys where feasible; cross‑chain standards and regulatory requirements mature.
This timeline is conservative and biased toward resilience; organizations that require higher assurance should accelerate it.
Migration challenges: wallets, custodians, HSMs, and UX
Transitioning a live ecosystem is nontrivial. Key challenges CTOs and custodians must plan for:
- Wallet compatibility and UX: Many consumer wallets and hardware wallets expect certain signature sizes and formats. Large PQ signatures can break existing UX flows (QR code lengths, gas estimation). Wallet SDKs must be upgraded and tested.
- Hardware Security Modules (HSMs): Custodians rely on certified HSMs. Vendors must add PQ primitives and pass certifications; procurement and rollouts take months to years.
- Backward compatibility: Chains will need to accept both old and new signature types for long periods. Hybrid signatures help, but they increase transaction size and verification costs.
- Key backup and secure rotation: PQ schemes may have larger keys or stateful properties (XMSS). Operational playbooks for backup, rotation, and disaster recovery must be rewritten.
- Performance and fees: Larger signatures increase storage and validation time. Layer‑1s must account for this in fee models so stablecoin transactions (e.g., USDC on ARC) remain economical.
Concrete steps for custodians and issuers:
- Perform a cryptographic inventory: map all private keys, their lifetimes, and where they are used.
- Test hybrid transactions on testnets and devnets with validators (e.g., Arc’s test infrastructure).
- Engage HSM vendors and obtain PQ firmware roadmaps.
- Update wallet SDKs and run UX audits for QR codes, mobile signing flows, and gas impacts.
- Coordinate with counterparties and regulators on migration timelines and contingency procedures.
Platforms such as Bitlet.app and other service providers should fold quantum risk into their operational roadmaps now, not later.
Policy and regulatory implications
Regulators are increasingly focused on operational resilience, auditability, and consumer protection for stablecoins. Quantum risk intersects with these themes in several ways:
- Disclosure requirements: Issuers may need to disclose cryptographic risk assessments and migration plans in stablecoin registrations or filings.
- Operational resilience standards: Rules may mandate redundancy or explicit timelines for migrating critical keys. Expect auditors to request evidence of PQ planning.
- Cross‑jurisdiction coordination: Because stablecoins and rails span borders, inconsistent PQ timelines across jurisdictions create systemic weak links. Harmonized standards will reduce systemic risk.
- Insurance and custody standards: Insurance underwriters and custodians will likely demand PQ‑capable infrastructure as a condition for coverage or custody of critical keys.
Policy makers will have to balance the cost of premature mass migration (which could harm interoperability and increase fees) against the catastrophic risks of inaction.
Practical recommendations for CTOs, custodians, and stablecoin issuers
- Start now with an inventory and threat model that explicitly includes quantum risk.
- Adopt hybrid signature schemes for critical keys as an intermediate step.
- Engage HSM and hardware wallet vendors about PQ support timelines; plan budgets for upgrades.
- Run test migrations on devnets; ask Layer‑1 providers (e.g., ARC) for migration guidance and compatibility matrices.
- Include quantum risk in regulatory filings, audits, and insurance conversations.
- Coordinate with counterparties and major validators to avoid unilateral hard forks or unexpected rejections of transactions.
Conclusion
Circle’s decision to integrate post‑quantum signature schemes into Arc and Naoris’ quantum‑aware mainnet launch mark a turning point: quantum resilience is migrating from theory into mainstream engineering for blockchain rails and national‑security projects. For CTOs, custodians, and stablecoin issuers, the right practical posture is proactive: inventory, hybridize, test, and coordinate. The costs of careful, planned migration are unquestionably lower than the systemic and reputational costs of being forced to scramble after a cryptographic break.
Sources
- Circle’s Arc post‑quantum announcement: https://cryip.co/circle-arc-blockchain-adds-quantum-resistant-security-for-stablecoin-finance?utm_source=snapi
- Naoris Protocol mainnet launch coverage: https://www.crowdfundinsider.com/2026/04/271318-naoris-protocol-mainnet-goes-live/