Uranium Finance Exploits: How $54M Vanished, $31M Was Seized, and What DeFi Teams Should Learn
Summary
Executive overview
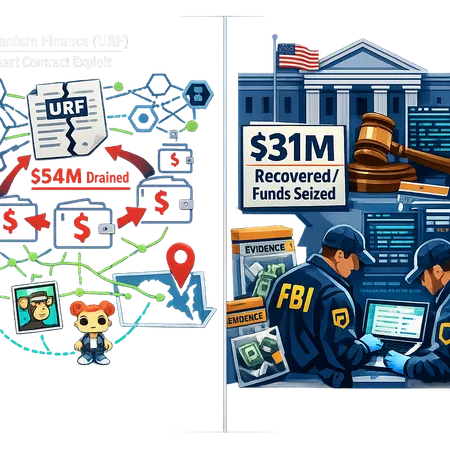
In mid-2021 and across subsequent investigations, Uranium Finance (ticker URF) suffered exploits that ultimately resulted in roughly $54 million of protocol funds being drained. U.S. prosecutors recently revived the case and announced a $31 million crypto recovery tied to the matter, and a Maryland individual has been formally charged in a case that carries substantial prison exposure. This explainer unpacks the timeline, how on-chain forensic work and traditional investigative tools combined to trace proceeds (even into digital collectibles), what the seizure and charges mean for DeFi actors, and concrete steps protocol teams and legal counsel should take going forward.
Timeline: How the Uranium Finance drains unfolded
Initial exploit(s): Audit and community reporting identified multiple vulnerabilities in Uranium Finance’s contracts, which attackers exploited to extract user liquidity and treasury funds over a short window. The total of those drains has been reported at about $54M across affected chains and pools.
Rapid mixing and conversion: After extraction, attackers typically used a predictable toolkit: swaps across DEXes, hops through cross-chain bridges, and on-chain mixers or services to obfuscate origin. In this case, investigators later documented movement into NFTs and collectibles as part of the conversion path.
Law enforcement intervention and revival: U.S. prosecutors revived the investigation with targeted legal actions that culminated in identifying wallet clusters, seizing on-chain assets worth approximately $31M, and charging a Maryland-based suspect.
The reconstruction above draws from public filings and reporting on the revived prosecution and recovery efforts, which show how long-term tracing can catch up with sophisticated laundering chains.
On-chain forensics: tracing the money from URF to collectibles
On-chain forensic teams and prosecutors used several complementary techniques:
Cluster analysis and address attribution. By linking transaction patterns, one-time-use wallets, and repeated counterparty addresses, analysts narrowed candidate clusters. Tools and manual analysis flagged wallets that consistently received funds originating from the URF exploit.
Token flow mapping. Investigators tracked swaps and bridge transfers, following the token trail across DEXes and wrapping/unwrapping steps to account for value movement in USD terms.
Behavioral signals and metadata. Patterns such as gas heuristics, reused nonces, or identical interaction sequences across wallets can betray a common operator even when privacy tools are used.
Asset conversion to collectibles. Critical to the case was the observation that proceeds were at times converted into NFTs and other on-chain collectibles. These purchases leave immutable records on-chain (token IDs, recipient addresses, timestamps), which provided concrete linkage between illicit proceeds and identifiable on-chain assets.
Cross-referencing off-chain data. Where possible, investigators matched blockchain records with exchange KYC, web3 marketplace accounts, or hosting logs to obtain real-world identifiers.
The combined effect: many obfuscation techniques slow down the trace, but they rarely erase the transaction history. Even moving value into an NFT doesn’t remove the chain evidence linking that asset to prior illicit flows.
The $31M seizure: what was recovered and how
U.S. authorities announced a seizure of roughly $31M in crypto assets tied to the Uranium Finance exploit. According to prosecutors, the assets were identified through the tracking methods above and then frozen or seized through legal process. Reporting indicates that the seized stash represented a substantial portion of the currently traceable exploit proceeds, though not the full $54M originally drained.
That recovery demonstrates two points:
- Large, on-chain movements leave a forensic trail that can be followed across swaps, bridges, and collectible purchases. Even when attackers attempt to diversify holdings, a critical mass can be identified and targeted.
- Seizing assets still requires legal authority and inter-agency cooperation; investigators paired blockchain evidence with legal mechanisms to obtain custody of wallets and funds.
For the public record and further reading on the seizure and revived charges, see coverage by Coinpaper and federal enforcement reporting.
Maryland suspect, charges, and penalties
Federal prosecutors in Maryland filed charges against a suspect alleged to be responsible for the Uranium Finance exploit. Media coverage of the case cites potential sentences that could reach approximately 30 years in federal prison, reflecting the seriousness of charges typically used in large-scale crypto theft prosecutions.
The revived prosecution underscores a shift in enforcement posture: agencies are willing to pursue old cases aggressively when new leads or forensic breakthroughs appear. The case illustrates how a combination of on-chain analytics and traditional investigation can produce arrests and indictments even years after an exploit.
For a closer look at the charging documents and sentence exposure, read the detailed reporting by The News Crypto and Crypto.News.
Legal prosecution in DeFi: what this case signals
This Uranium Finance matter is instructive for several reasons:
Prosecutors will follow the money. The public seizure shows that converting stolen value into non-fungible tokens or routing through multiple protocols does not guarantee immunity. Immutable records can tie assets back to original thefts.
Cross-border puzzles remain—but cooperation helps. Many DeFi exploits involve cross-chain and cross-jurisdiction movement. While investigators still face hurdles in international cooperation, the U.S. seizure shows domestic legal tools are powerful when offenders touch U.S.-linked infrastructure or transact with platforms subject to U.S. jurisdiction.
Vulnerable protocols can attract detective focus. High-profile hacks create public interest and allocate investigative resources; teams should assume that large thefts will be pursued vigorously and that evidence will be preserved.
Recovery is partly technical, partly legal. Forensics identify assets and addresses; prosecutors and courts provide the mechanism to freeze or seize. Protocols that can quickly present forensic reports and civil claims improve the odds of recovery.
This convergence of chain analysis and prosecutorial action is increasingly common in big exploit cases, and it should shape how protocols prepare for incidents.
Implications for DeFi security audits and cross-border enforcement
The Uranium Finance exploit and recovery highlight several audit and enforcement takeaways:
Audits are necessary but not sufficient. Formal code audits should be complemented by continuous monitoring, bounty programs, and red-team exercises that simulate economic attacks, oracle manipulation, and complex flash-loan vectors.
Assume rapid monetization paths. Auditors must analyze not only reentrancy and access control bugs but also how fast an attacker can swap or bridge stolen funds; audit scopes should include economic and composability risk assessments.
Monitor post-deployment flows. Protocol teams need real-time alerts for abnormal treasury or pool movements. The faster suspicious flows are flagged, the better the chance that some value remains recoverable.
Cross-border enforcement will grow more capable. As investigators become savvier with on-chain tracing, cross-jurisdiction collaboration and legal tools (mutual legal assistance treaties, asset restraint orders) will increasingly enable seizures or cooperation across borders.
Collectible purchases are not a safe harbor. Purchases of NFTs or in-game items leave on-chain provenance and marketplaces may cooperate with authorities when presented with subpoenas or legal orders.
These points should inform both technical audit scopes and legal incident response playbooks.
Recommended steps for protocols to reduce criminal exposure and aid recovery
For security leads, legal counsel, and protocol teams, the Uranium Finance case suggests a practical checklist:
Harden contract design and review attack surfaces. Go beyond standard audits: include economic simulations, flash-loan attack modeling, and adversarial reviews. Consider third-party formal verification for critical modules.
Implement treasury safety measures. Use multi-signature wallets, time locks for large transfers, whitelists for one-off administrative actions, and pause functionality that can be activated by an emergency committee.
Maintain comprehensive logging and monitoring. Capture on-chain telemetry, maintain a transaction history for treasuries, and subscribe to alerts for large swaps or bridge transfers involving protocol wallets.
Prepare legal relationships in advance. Pre-arranged points of contact with law enforcement, a documented incident response counsel, and templates for forensic reports accelerate recovery requests and evidence preservation.
Use strong bounty and disclosure programs. Encourage security researchers to report vulnerabilities by offering competitive bounties and clear disclosure channels. Rapid resolution often prevents the exploitation or reduces its scale.
Coordinate with on-chain forensic vendors. Establish relationships with reputable firms that can produce court-ready chain analysis. Evidence formatted and authenticated for legal use shortens the path to seizure.
Consider asset recovery insurance and contingency funds. While insurance markets are imperfect, reserved funds and policies can reduce user loss and provide liquidity while legal recovery progresses.
Limit single points of failure in composability. Where possible, avoid designs that permit draining of multiple pools through a single call; compartmentalize risk.
Educate governance participants. Ensure token holders and multisig signers understand the legal and operational steps needed during an incident, and create playbooks that assign responsibilities.
Preserve on-chain evidence. Do not attempt unilateral vigilante recoveries (such as flooding or counter-attacks). Work with counsel and reputable forensic partners so that evidence remains admissible and legally useful.
Leveraging these measures helps protocols reduce the chance of a catastrophic loss and improves the chance that any stolen assets can be tracked and recovered. Practical preparedness is a force multiplier for both technical and legal response.
Case nuances and open questions
Full recoverability is rare. The $31M recovery is meaningful but does not match the total alleged drain. Assets may be dispersed across chains, converted to fiat, or held in jurisdictions with limited cooperation.
Attribution thresholds vary. Linking an individual to on-chain activity requires a mix of technical and human intelligence. Prosecutors must show beyond a reasonable doubt that a defendant controlled the addresses used.
Market and community responses matter. How a protocol responds publicly (transparency, compensation plans, legal action) can influence both user trust and the vigor of investigative partners.
Regulatory ripple effects. High-profile prosecutions encourage exchanges and marketplaces to tighten AML controls on NFT purchases and large OTC trades, which indirectly raises the cost of laundering for attackers.
Practical checklist for immediate post-exploit action (for incident response teams)
- Freeze and snapshot: Immediately snapshot protocol state and freeze admin keys where possible. Preserve evidence (logs, deployment artifacts).
- Engage counsel: Retain counsel with crypto incident experience and notify local law enforcement contacts.
- Activate forensics: Hire an on-chain analysis firm for a court-ready report showing fund flows and asset locations.
- Notify counterparties: Alert bridges, CEXs, and major DEX operators with indicators of compromise and wallet addresses.
- Prepare governance: Convene multisig signers and emergency committees with predefined authorities and public communication templates.
- Coordinate communications: Provide clear, factual public updates that avoid speculation and preserve legal positioning.
Conclusion: what DeFi teams should take away
The Uranium Finance case underscores a simple reality: on-chain does not mean untraceable, and an exploit is both a technical incident and a legal one. Robust security engineering, rapid monitoring and response, forensic readiness, and pre-planned legal relationships materially improve the likelihood of mitigation and recovery. Teams that mix strong technical design with legal preparedness — and that treat incident response as cross-functional work — will be better positioned when (not if) a high-stakes incident occurs.
For security leads and counsel, the practical lesson is to invest in prevention and recovery equally: audits and automated defenses reduce risk, but forensic partnerships and legal playbooks convert tracing work into real-world recoveries. Tools and platforms across the ecosystem, including monitoring services and marketplaces that enforce AML policies, are also adapting; companies like Bitlet.app can be referenced for how custody and movement tools are evolving in this climate.
Sources
- U.S. revives Uranium Finance hack case with Maryland charges and $31M seizure — Coinpaper
- Uranium Finance hacker charged in $54M DeFi exploit, faces 30-year sentence — The News Crypto
- U.S. charges Maryland man in $54M Uranium Finance exploit case — Crypto.News
For further reading on on-chain tracing techniques and practical incident playbooks, see materials from major forensic firms and recent enforcement guidance from U.S. prosecutors. If you're leading a protocol security team, consider formalizing the checklist above with both internal and external partners and keeping those relationships active between incidents.
For context on broader market dynamics and historical exploit patterns, consult prior case studies on token rug pulls, bridge exploits, and NFT laundering — and follow updates in the DeFi coverage that track emerging tactics.