Quantum‑Resistant Cryptocurrencies: Practical Upgrade Paths for BTC and DOGE
Summary
Why post‑quantum planning is now a practical engineering problem
The cryptographic community has long warned that general‑purpose quantum computers will eventually undermine widely used public‑key systems such as ECDSA and Ed25519. That threat—quantum resistance—is driving two parallel efforts inside the crypto industry: (1) standardizing post‑quantum signature schemes and (2) designing how blockchains can migrate to new primitives without destroying value or causing chain splits.
For blockchain engineers and wallet vendors this is not an abstract debate. Protocols like BTC and DOGE use elliptic‑curve signatures that, given a full‑scale quantum adversary, could be broken. The current consensus among researchers is that the arrival of capable quantum hardware is not imminent, but the lead times for updating infrastructure—secure firmware on hardware wallets, exchange cold storage practices, and wide wallet adoption—are measured in years. That makes planning urgent but measured: act now to design migration paths, test hybrid deployments, and avoid reactive, rushed upgrades later.
Research proposals and signature scheme tradeoffs
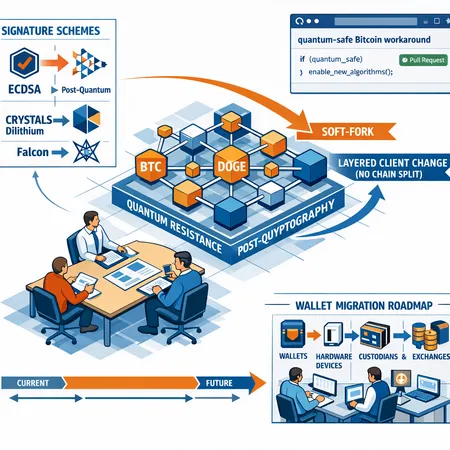
Academic and standards bodies have produced several families of post‑quantum signatures: hash‑based (XMSS, SPHINCS+), lattice‑based (CRYSTALS‑Dilithium, Falcon), multivariate and code‑based approaches. Each comes with tradeoffs:
- Signature size and public key size: Hash‑based and some lattice schemes can produce much larger signatures and keys than ECDSA. SPHINCS+ signatures are large—hundreds to thousands of bytes—whereas Dilithium and Falcon aim for smaller signatures, though still larger than ECDSA.
- Verification and signing cost: Lattice schemes generally have lower verification cost than hash‑based alternatives but may require more complex math that hardware wallets must support.
- Statefulness: Certain hash‑based schemes are stateful (e.g., XMSS), which complicates key management—reusing a key can catastrophically break security.
- Confidence and standardization: NIST’s PQC process has advanced lattice‑based and hash‑based finalists; using NIST‑standardized options reduces long‑term risk but requires time to settle.
For blockchain use we typically look for: stateless schemes (or carefully managed stateful schemes), compact signatures, fast verification, and robust standards. That’s why many blockchain projects favor lattice candidates like CRYSTALS‑Dilithium or hybrid constructions that combine classical ECDSA/EdDSA with a post‑quantum signature.
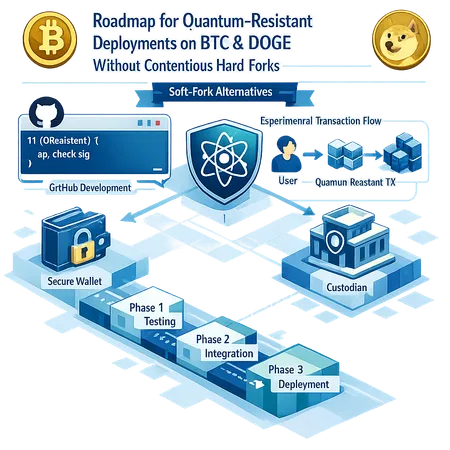
The GitHub 'quantum‑safe Bitcoin' workaround — what it is and what it proves
A recent community GitHub project, described in technical coverage, proposes a no soft‑fork path to improve Bitcoin’s quantum resistance by layering client behaviour and leveraging existing script and witness structures rather than changing consensus rules directly. The idea is pragmatic: instead of introducing new opcode semantics via a soft fork, developers can construct transaction patterns and wallet policies that move funds into outputs that are spendable with post‑quantum proofs alongside classical proofs. Coverage of that project appears in a technical breakdown that explains the approach and its limitations (DailyCoin analysis).
At a high level the workaround demonstrates two key concepts: first, it is possible to create hybrid spending conditions—leaves in a Taproot‑style structure or specially crafted script outputs—that accept either a classical or a post‑quantum signature. Second, by keeping the change within client policy and transaction construction, early adopters can move coins to hybrid addresses without requiring miners or full‑node consensus changes. That reduces coordination requirements while providing real cryptographic protection for migrated funds.
This approach is not a silver bullet. It relies on software ecosystem adoption: wallets must generate and recognize hybrid addresses, exchanges and custodians must accept deposits to these addresses, and hardware wallet firmware must be updated to support the new signing primitives. It also inherits practical limits—larger transaction sizes, potentially higher fees and new UX complexities such as managing stateful keys and edge cases for legacy wallet recovery.
Dogecoin experiments: early engineering proof‑of‑concepts and lessons
Dogecoin engineers have been experimenting with quantum‑resistant transactions in test settings to understand performance and integration costs. Reporting on those efforts highlights two themes: experimentation with hybrid keys and pragmatic measurement of signature sizes and verification times on constrained devices (report).
The Dogecoin tests focused on integrating post‑quantum signature schemes into existing transaction flows to evaluate real‑world impacts: mempool acceptance, wallet UX, and hardware signing constraints. Engineers tend to try hybrid constructions—combining the existing ECDSA/Ed25519 signature with a post‑quantum signature in the same spending condition—so that funds are safe as long as either scheme remains secure during a transition window. These experiments are invaluable: they surface implementation gotchas (padding, serialization, signing formats), reveal how much extra data goes into transactions, and expose compatibility issues with existing nodes and light wallets.
For practitioners this is the model to follow: realistic, testnet‑level experiments to measure tradeoffs before pushing broader adoption. Projects that skip this step risk breaking user expectations or overloading hardware devices with infeasible cryptographic workloads.
Soft‑fork vs. layered client changes: a nuanced tradeoff
There are two dominant upgrade strategies available to blockchains: protocol changes enforced by consensus (soft forks/hard forks) and layered client changes that rely on wallet + service adoption without changing consensus rules.
Soft Forks / Consensus Changes: A soft fork that enforces new signature types gives the strongest guarantees: no compliant node can accept non‑conforming transactions once the rule activates. The downside is clear: coordination and risk. Activating a soft fork requires broad node operator and miner cooperation, code audits, and a long rollout to avoid chain splits. Soft forks can also be risky if the new verification rules are complex or introduce performance problems.
Layered Client Changes / Opt‑In Migration: Layered approaches—like the GitHub workaround—allow opt‑in migration by enabling wallets to create hybrid or alternative outputs and by encouraging custodians to accept them. The advantage is speed and low risk of chain split. The downside is the reliance on ecosystem adoption: funds left on legacy addresses remain vulnerable, and non‑adopters may be unable to process or validate new constructs if they diverge from typical patterns. Additionally, because the consensus rules haven’t changed, miners still accept legacy invalidation vectors and are not required to treat the new scripts differently.
For BTC and DOGE, a pragmatic path is often combined: start with layered client changes to protect early adopters, run extensive testing and interop trials, then consider a later, well‑planned soft fork if it becomes necessary to enforce a new standard across the network.
Custodians, exchanges and early adopter implications
Custodians and exchanges are high‑value targets and must be first in migration planning. Their decisions determine whether migrated outputs are accepted by the broader market. Practical considerations include:
- Key rotation strategy: Move hot‑wallet and cold‑storage funds into hybrid or post‑quantum addresses on a staged schedule. Never migrate all funds at once.
- Replay and deposit handling: Update deposit detection systems to recognize new address formats or script patterns so customer deposits are credited properly.
- Auditability and legal compliance: Maintain auditable key management logs and ensure multi‑party signing systems (HSMs, MPC) support new algorithms. Regulatory auditors will want to see continuity of custody and secure migration practices.
- Interoperability testing: Run interoperability tests with major wallet providers and hardware vendors. Exchanges should publish upgrade schedules and testnet addresses.
Exchanges and custodians may prefer to delay full migration until hardware wallets and standards stabilize, but they should prepare pilots: a small percentage of cold storage on hybrid addresses, thorough SOPs for recovery, and transparent customer communication.
Wallets and hardware devices: migration timeline and practical steps
A realistic migration timeline has overlapping phases:
- Research & Standardization (0–24 months): track NIST PQC outputs and IETF/industry drafts. Select recommended schemes and finalize serialization formats.
- Prototype & Test (6–18 months): implement libraries, run Dogecoin‑style experiments on testnets, measure signing/verification costs on hardware devices.
- Client & Firmware Updates (6–36 months): roll out wallet software and hardware firmware that supports hybrid signing, key generation and address formats.
- Opt‑In Migration & Pilots (6–24 months): exchanges, custodians and advanced users begin moving funds to hybrid addresses. Monitor for issues and update recovery tooling.
- (Optional) Consensus Enforcement (24–60 months): if necessary and coordinated, plan a soft fork to enforce new rules once the ecosystem is ready.
Concrete wallet migration steps for vendors and CTOs:
- Implement hybrid signatures (classical + post‑quantum) so users retain safety even if only one side is broken.
- Update address formats to clearly indicate hybrid/post‑quantum outputs and communicate UX changes to users.
- Build key rotation and recovery tooling that supports exporting/importing post‑quantum public keys, with attention to stateful schemes.
- Coordinate with hardware vendors early: many devices have limited flash/compute budgets. Benchmarks from Dogecoin experiments should be used to set firmware release priorities.
- Provide migration SDKs and test vectors so custodians and exchanges can integrate quickly.
Recommendations and an implementer’s checklist
For CTOs, wallet vendors and blockchain engineers building migration roadmaps, here is a prioritized checklist:
- Adopt a hybrid signing strategy for early migrations to mitigate immediate risk without breaking compatibility.
- Start interoperability tests now—use testnets and run the same scenarios described in public experiments for BTC and DOGE; emulate exchange deposit flows and hardware signing.
- Inventory your key material and classify wallets by exposure (hot, warm, cold). Migrate high‑risk hot wallets first.
- Engage hardware wallet manufacturers to benchmark chosen PQC schemes and get firmware timelines.
- Publish an upgrade calendar and migration playbooks for customers, and coordinate pilots with custodial partners.
- Track standards: NIST PQC outputs, IETF proposals and community GitHub projects; incorporate proven libraries rather than ad‑hoc implementations.
- Keep user UX simple: hide signature complexity from end users where possible and provide clear recovery instructions.
Platforms like Bitlet.app and other P2P services should incorporate migration timelines into their operational roadmaps and provide wallets that can detect hybrid or post‑quantum outputs.
Closing perspective: plan now, move deliberately
Quantum‑resistant cryptography is becoming an operational engineering problem. The good news is that community work—ranging from academic proposals to practical GitHub proof‑of‑concepts and Dogecoin experiments—shows upgrade paths that do not require immediate, risky chain splits. The cost is coordination: vendors, custodians and node operators must test, iterate and adopt hybrid approaches first, then consider stricter enforcement later if the ecosystem demands it.
Engineers should balance urgency with prudence: prioritize hybrid deployments, measure real device performance, and plan staged migrations. That way, networks like Bitcoin and Dogecoin can materially improve their posture against future quantum threats without breaking the systems users depend on today.
Sources
- DailyCoin — Quantum‑Safe Bitcoin No Soft Fork: a new workaround hits GitHub: https://dailycoin.com/quantum-safe-bitcoin-no-soft-fork-a-new-workaround-hits-github/
- U.Today — Dogecoin experiments with quantum‑resistant transactions: https://u.today/dogecoin-experiments-with-quantum-resistant-transactions-doge-engineer-weighs-in?utm_source=snapi