Quantum-Safe Bitcoin: StarkWare’s No-Upgrade Idea, Alternatives, and What Custodians Should Do
Summary
Why quantum-safety is back on the table
Discussion about quantum computers and Bitcoin is not new, but it has recently become more concrete because of fresh, public proposals and vocal industry reactions. One prominent idea — put forward in public writing and covered widely — proposes a way to make Bitcoin quantum-resistant without changing the protocol, while others push for standard, protocol-level migrations to post-quantum signature schemes. Industry voices have reacted strongly on both sides: some call new defensive designs a practical step, others warn they are stop-gap or last-resort measures. For many readers tracking BTC security, this debate matters because it shifts the conversation from hypothetical futurism to operational decisions today.
Public responses have been visible: commentators like Samson Mow have pushed back against what they see as overblown quantum FUD, while technical outlets and analysts have dug into feasibility and cost. See the recent industry reactions summarized by U.Today for one example of the public pushback and context.
Two leading public approaches
StarkWare’s GPU‑heavy, no-protocol-change scheme
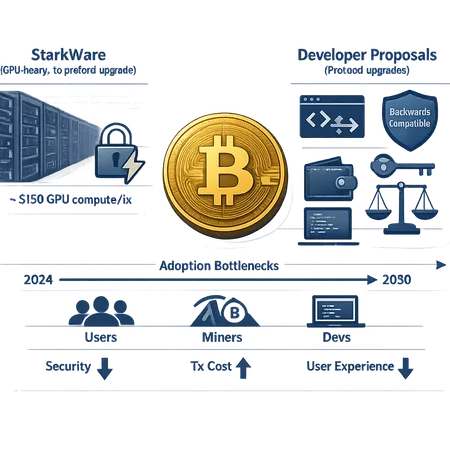
StarkWare and related commentary have described an approach that, crucially, does not require a Bitcoin protocol upgrade to add a layer of post-quantum defense. The idea is to produce an off-chain or pre-signed, computationally expensive proof or attestation that changes the effective security model of spending an output — effectively making it much harder for a quantum adversary to derive the signing key in time to steal funds. Proponents argue this can be deployed immediately because it doesn't require consensus changes.
Reportedly, however, this method is compute-intensive. Recent write-ups cite a rough order-of-magnitude cost: around $150 in GPU compute per quantum-safe transaction (figures come from the public descriptions and coverage; more precise numbers will vary with hardware prices and optimizations). Those cost and latency characteristics shape who can reasonably use the method and how often.
Coverage and analysis: Unchained Crypto published a deep explainer of this scheme and its GPU-cost claims, while CoinSpeaker and others summarized the key practical implications. The Block called the proposal a potential "last-resort measure," noting adoption concerns and tradeoffs in real-world rollout.
Protocol‑level post‑quantum migrations and developer proposals
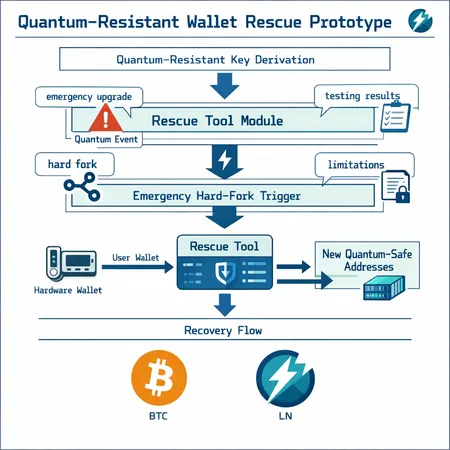
The alternative family of approaches is the more conventional path: change the crypto primitives used for signatures on-chain (or add hybrid signatures that combine secp256k1 with a post-quantum scheme). That can mean introducing new address types, soft forks or hard forks, and new wallet standards based on lattice-based, hash-based, or code-based post-quantum algorithms (for example, signature schemes like Dilithium, Falcon, or stateless hash-based signatures in principle).
These proposals trade backward compatibility and implementation complexity for clearer long-term security: once adopted, every new signature would be resilient against both classical and (targeted) quantum attacks, without per-transaction heavy compute. But protocol changes introduce coordination, long timelines, and compatibility headaches for wallets, exchanges, miners, and hardware devices.
Technical tradeoffs: security model, UX, and costs
Security model
- StarkWare-style: The security assumption shifts from changing the consensus-layer primitives to protecting the lifecycle of keys and outputs by adding expensive-to-forge attestations. It is pragmatic and incremental, but it places trust in the efficacy of the added computations and in the attack model (for example, whether a quantum attacker can still act inside the window between a transaction broadcast and confirmation).
- Protocol-level: Changing the signature scheme gives a more uniform cryptographic guarantee. A properly selected and standardized post-quantum primitive resists known quantum algorithms without relying on operational mitigations.
Backward compatibility
- No-upgrade schemes can be applied selectively by wallets and custodians to specific outputs with no network upgrade required. That makes them attractive for rapid deployment.
- Protocol upgrades require broad ecosystem coordination. Even soft forks can be contentious and take years to reach sufficient deployment and testing.
Transaction cost and UX
- The StarkWare proposal’s headline number (around $150 of GPU compute per protected transaction) matters because it directly hits user wallets and custodial cost models. That cost is an incremental operational charge on top of standard Bitcoin fees, and it can change UX (longer latencies, requirement to perform heavy local computation, or rely on third-party attestation services).
- Protocol-level post-quantum signatures likely increase transaction size (larger signature bytes than secp256k1 for many PQ schemes), which raises on‑chain fee costs per transaction but avoids repeated heavy per-transaction GPU work. UX tradeoffs include initial device support and migration paths for existing keys.
Developer and miner impacts
- For miners, a no-upgrade scheme usually has minimal direct protocol-level effects: miners still validate transactions as before. Indirectly, if quantum-safe transactions become more expensive or slower, fee market dynamics could change.
- For developers and wallet vendors, no-upgrade schemes require integrating heavy computation or relying on services to produce attestations. Protocol upgrades require implementing new crypto stacks, updating hardware wallets, and supporting migration tooling.
Adoption bottlenecks and realistic timelines
Adoption bottlenecks
- Consensus friction: Any protocol change to Bitcoin must cross a high bar of community coordination, testing, and opt-in deployment. Expect multi-year timeframes for significant on-chain changes.
- Custodial inertia: Exchanges, custodians, and custodial wallets must test, certify, and adjust insurance and operational processes before enabling any new protective flows.
- Cost and UX: Per-transaction GPU costs or larger on-chain signatures will change business models, especially for high-throughput services and low-value transfers.
- Standardization: The community needs interoperable standards for post-quantum keys and address formats; until that exists, adoption will be fragmented.
Realistic timelines
Quantum-resistant posture is a multi-year effort. Most cryptographers and industry analysts estimate that useful, large-scale quantum computers capable of breaking secp256k1 are not a one-year threat — more likely measured in years to a decade — but uncertainty is significant. Because ecosystem migration and standardization take time, pragmatic planning should begin now even if decisive technical changes are not immediate.
As reported coverage emphasizes, some participants view measures like StarkWare’s as stop-gaps or emergency measures rather than final answers; others treat them as practical short-term defenses while standards evolve. The Block framed similar proposals as potential last-resort options while debating real deployment costs and implications.
Why the debate reignited now (and how to read the FUD)
Two factors have sharpened the conversation: new, publicly described proposals that make deployment seem more actionable; and high-profile commentary from industry figures that brings the issues to broader attention. That combination creates a feedback loop: public proposals invite scrutiny, which invites headlines, which invites policy and custody teams to ask whether they need to act.
It’s important to separate sensible risk management from panic. Public figures and outlets have pushed back against alarmist narratives — for example, Samson Mow and others have criticized claims that an imminent breach is inevitable — but constructive skepticism should not become complacency. Practical mitigation (better key management, multisig, migration planning) is sensible today even if the worst-case quantum scenario remains uncertain.
Practical steps for holders, custodians, and miners
For custody teams and technically literate holders, prioritize operational controls and coordinated testing rather than jumping to a single technical fix.
Immediate actions (weeks to months)
- Inventory and classify keys: Know which keys control hot funds, warm wallets, cold storage, and long-term vaults. Focus the most conservative protections on long-term holdings.
- Enforce key rotation where practical and document rotation policies. Rotation reduces the exposure window from any future cryptanalytic advance.
- Prefer multisig and distributed custody: Multisignature schemes (with geographically and jurisdictionally separated signers) raise the bar for any attacker, quantum or otherwise.
- Tighten operational procedures: Minimize key reuse, restrict online signing for large outputs, and enforce stronger physical security for cold keys.
Near-term technical steps (months to one year)
- Test hybrid and no-upgrade options in a controlled environment: If a custodial provider wants to trial a StarkWare-style attestation or a hybrid signature approach, do it on a testnet or internal sandbox first and measure cost, latency, and failure modes.
- Coordinate with wallet vendors and exchanges: Custodial providers should discuss migration and support with third-party wallets early — interoperability is crucial.
- Update incident response and insurance: Talk to insurers about how quantum defenses are treated in policy language and adjust SLAs and coverage if needed.
Longer-term planning (1–5 years)
- Follow standardization: Participate in (or track) efforts to standardize post-quantum address types and signature formats for Bitcoin and related tooling.
- Plan staged migration: If the ecosystem moves toward protocol-level changes, prepare a migration playbook and technical roadmap for how to move funds with minimal disruption.
- Budget for increased costs: If you adopt GPU-based defenses or expect larger on-chain signatures, include these costs in product pricing and fee models.
A practical note: services like Bitlet.app and other custody platforms will need to balance customer UX against the costs and complexity of any quantum defense. Coordinated industry testing and transparent disclosure will be important.
How miners and node operators should think about this
- Miners: No immediate change is required unless the community adopts a protocol-level post-quantum scheme. Indirect effects — changes in fee dynamics or new transaction types — could influence block templates and relay policies.
- Node operators: If a soft-fork or new standard is proposed, node operators will need time to upgrade. Where possible, run experimental implementations in parallel to measure performance and compatibility.
Bottom line: incremental preparedness, not panic
The current set of proposals offers different tradeoffs. StarkWare-style no-upgrade defenses are interesting because they can be deployed without a Bitcoin-wide protocol change, but they bring per-transaction GPU cost and UX penalties and are best viewed as operational mitigations rather than definitive long-term fixes. Protocol-level migration to vetted post-quantum signature schemes gives a more uniform guarantee but will demand years of coordination, testing, and ecosystem changes.
For custody teams and holders, the sensible path is to prioritize key hygiene, multisig, staged testing of defenses, and active engagement with standardization efforts. Treat the present moment as an early-warning phase: plan, test, and harden practices now so you won’t be forced into rushed, expensive migrations later.
For further technical reading and contemporaneous coverage of the proposals and reactions, see the write-ups and commentaries listed in Sources below. For many practitioners, the next practical steps are operational and policy-oriented — and those can (and should) be implemented today.
Sources
- StarkWare scheme overview and GPU compute cost discussion: Unchained Crypto
- The Block coverage and discussion of adoption concerns: The Block
- Short explainer summarizing the claim Bitcoin can be made quantum-safe without protocol upgrades: CoinSpeaker
- Industry reaction and commentary (Samson Mow response): U.Today
(Internal note: this article mentions Bitcoin and wider ecosystem implications including DeFi.)