Quantum‑Resistant Upgrades for Live Chains: Practical Paths Without Hard Forks
Summary
Why post‑quantum preparedness matters now
Quantum‑resistant and post‑quantum cryptography are no longer purely academic concerns for crypto product leads. While large‑scale fault‑tolerant quantum computers that break ECDSA/Ed25519 remain uncertain in timing, the window for defensive action is long and the stakes are huge: stolen private keys are permanent and blockchains are immutable. Practical defenses can be rolled out incrementally to reduce risk without fracturing networks.
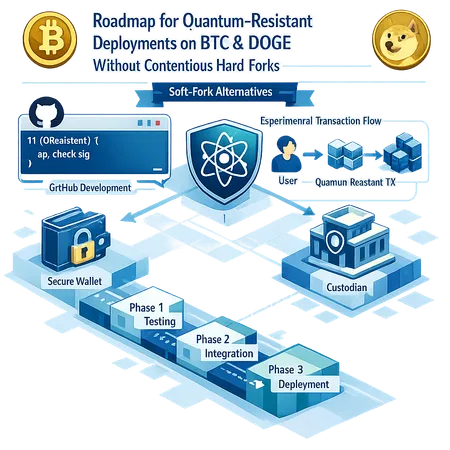
For teams working on BTC and DOGE, the question is not just if to upgrade, but how to do it without a contentious hard fork. Two recent developments — a GitHub workaround that aims to bring quantum‑safe Bitcoin closer without a soft fork and experimental quantum‑resistant transactions in Dogecoin — point to realistic, deployable options based on wallet and script innovations rather than consensus rule changes (DailyCoin coverage; U.Today report on Dogecoin experiments).
The GitHub workaround for Bitcoin: principles and tradeoffs
At a high level, the GitHub workaround reported in the community aims to avoid a soft fork by using existing script and key‑management primitives to migrate UTXOs into post‑quantum‑protected forms. The idea is pragmatic: leverage wallet‑level coordination and already‑available opcodes and spending paths instead of changing consensus. That reduces governance risk but introduces operational complexity.
Key design themes in a workaround of this type:
- Wallet‑orchestrated migrations: wallets construct and broadcast special transactions that lock funds under spending conditions tied to post‑quantum keys or hybrid signatures.
- Script‑level enforcement: instead of adding new opcodes, the approach uses Taproot or existing multisig/script templates to embed commitments or recovery paths that expect different signature validation off‑chain.
- Opt‑in safety: only users who choose to migrate are affected, avoiding a forced consensus change.
Tradeoffs to understand: script‑level workarounds keep consensus stable but often require more operational coordination, larger transactions, and careful key handling. They also shift the migration burden onto wallets and custodians — which is both an advantage (no protocol vote needed) and a risk (fragmented adoption, UX headaches).
Dogecoin experiments: what’s different and why it matters
Dogecoin developers experimenting with quantum‑resistant transactions demonstrate that smaller, active communities can be useful testbeds for new patterns. The Dogecoin work reported by U.Today shows engineers prototyping ways to accept post‑quantum signatures in a way that's minimally invasive to the running node software while allowing early adopters to transact with more durable protections.
The lessons for larger networks are practical:
- Lightweight experimental deployments can validate signature formats, size tradeoffs, and compatibility with hardware wallets.
- Developer buy‑in and clear migration documentation accelerate adoption: Dogecoin's approach centers on engineering experiments rather than governance drama.
- Results from experimental chains inform safer rollouts on conservative networks like Bitcoin.
Implications for wallets and custodians
Wallets and custodians are the front line for post‑quantum defense. Any no‑soft‑fork approach pushes a lot of technical work to these actors. Key implications include:
Hybrid signatures are a pragmatic first step. Use both classical (ECDSA/secp256k1 or Schnorr) and post‑quantum signatures together so funds remain spendable under either primitive during a transition period. Hybrid schemes greatly reduce the risk of single‑point failure while algorithms and standards stabilize.
Key lifecycle and rotation must be rethought. Custodians need procedures for generating, storing, rotating, and recovering post‑quantum keys. Hardware security module (HSM) vendors must add support for selected PQC algorithms and safe formats for backups and export.
Signature sizes and fee economics matter. Many post‑quantum signature schemes (especially stateless hash‑based ones) have larger signatures. That affects on‑chain fees, QR encoding for UX, and hardware wallet display constraints. Teams should benchmark signature sizes and measure fee impact under realistic transaction mixes.
Interoperability testing is mandatory. Multisig setups with both classical and PQC keys, watch‑only configurations, and third‑party transaction builders need thorough integration tests to prevent accidental fund lockups.
Custodial policy and legal controls. Custodians should update SLA and custody agreements to reflect new cryptographic standards, migration windows, and client consent models.
UX and migration hurdles: what users actually face
Even technically sound migrations fail when UX is ignored. Expect these common hurdles:
- Complex opt‑in flows. Users may be uncomfortable generating new keys or moving funds. Smooth, well‑explained flows with fail‑safe fallbacks are essential.
- Backup and recovery friction. New private key formats and longer seeds require rethinking backup UX. Migration assistants should automate export/import into secure formats and provide clear instructions for hardware wallets.
- Hardware wallet compatibility. Many hardware devices will need firmware updates to support PQC algorithms like Dilithium or Kyber. Coordinating these updates across vendors is non‑trivial.
- Fee transparency. Larger signature payloads raise fees. Present clear cost estimates and, where possible, batch or aggregation techniques to reduce per‑user costs.
- Trust and education. Users must understand why migration is needed and how it protects long‑term value. Educational tooling, in‑app notifications, and staged rollouts build confidence.
Bitlet.app — and other product teams — should factor these UX constraints early in their technical roadmap.
Practical patterns for no‑hard‑fork deployment
Below are recommended patterns that balance security, deployability, and user impact:
- Hybrid signatures at the wallet level
- Implement transaction formats that require both a classical and a PQC signature (or accept either during transition) and coordinate migration UTXOs that move funds into hybrid‑protected scripts.
- This offers gradual protection without protocol change.
- Script‑based opt‑in migration
- Use Taproot or existing script templates to create outputs that can be spent via a post‑quantum path under certain conditions while preserving the classical path for fallback.
- Advantage: no consensus upgrade. Drawback: requires careful wallet coordination.
- Layer‑2 first deployments
- Deploy PQC on Lightning‑style channels and other layer‑2s, then backfill lessons into base layer migration plans. Layer‑2s can act as a testbed and reduce on‑chain fee pain.
- Wallet/SDK libraries and standards
- Ship battle‑tested SDKs that encapsulate PQC operations, signature assembly, and recovery logic. Avoid ad‑hoc implementations across wallets.
- Custodian blueprints
- Provide custodial playbooks for generating PQC keys in HSMs, co‑signer procedures, and emergency recovery. Include legal and audit checklists.
A pragmatic roadmap for teams (quarterly milestones)
Quarter 0 — Assessment & decision
- Inventory exposure: quantify UTXOs, custodial holdings, and reuse patterns that increase risk.
- Select candidate PQC algorithms (prefer NIST‑approved options such as CRYSTALS‑Dilithium for signatures and CRYSTALS‑Kyber for KEMs) and create threat models.
Quarter 1 — Prototype & toolchain
- Build wallet prototypes supporting hybrid signatures and a reference transaction format.
- Engage hardware wallet vendors to prototype firmware support.
Quarter 2 — Testnet experiments
- Run controlled testnet migrations and user trials. Learn signature size, fee impact, and UX issues.
- Publish migration SDKs and guides for custodians.
Quarter 3 — Opt‑in mainnet rollout
- Open an opt‑in migration window for power users and custodians. Monitor and iterate on issues in real time.
- Encourage layer‑2 and exchange participation.
Quarter 4 — Broader adoption & audit
- Expand tooling to mainstream wallets, run third‑party cryptographic audits, and produce migration metrics.
- Consider whether a future consensus change is still needed based on adoption and threat posture.
Final considerations and governance
- Avoid binary thinking: immediate hard forks are not the only path. Script‑level and wallet‑level techniques can buy safety while the ecosystem converges on standards.
- Maintain transparency: publish migration plans, open‑source SDKs, and audit results so custodians and users can make informed choices.
- Measure success by adoption and incident reduction: the goal is practical risk reduction across BTC and DOGE ecosystems, not a one‑time technical victory.
For teams researching implementable, short‑to‑medium‑term defenses against quantum risk, the combined evidence from GitHub‑led Bitcoin workarounds and Dogecoin experiments points to a realistic toolkit: hybrid keys, script migrations, layer‑2 testbeds, and coordinated custodian playbooks. Product leads should prioritize integration testing, hardware vendor coordination, and clear migration UX to make post‑quantum resilience a deliverable feature, not a theoretical ideal.