Quantum‑Resistant Wallet Rescue: Lightning Labs CTO’s Prototype and the Practical Debate Over Bitcoin’s Quantum Risk
Summary
Why quantum risk matters — and why it’s debated
Quantum computing gets headlines because of its theoretical ability to break some widely used public‑key algorithms. For BTC holders and product leads the relevant question is practical: could a sufficiently capable quantum adversary derive private keys from on‑chain public keys quickly enough to steal funds before the community implements a fix? That question splits into two threads: the technical rescue problem (how to move funds quickly if an exploit becomes imminent) and the risk framing (how likely and how soon such a quantum capability is).
The Lightning Labs CTO recently published a prototype “wallet rescue” tool designed to address the first thread: a mechanism to recover funds if the network had to perform an emergency upgrade to thwart quantum attacks. The prototype and the surrounding discussion force product teams to think through operational playbooks, even if some experts — including Michael Saylor — argue quantum risk is currently overblown and far from an immediate existential threat to BTC. For many teams the right posture is practical preparedness and cryptographic agility, not alarmism.
What the wallet rescue prototype is trying to solve
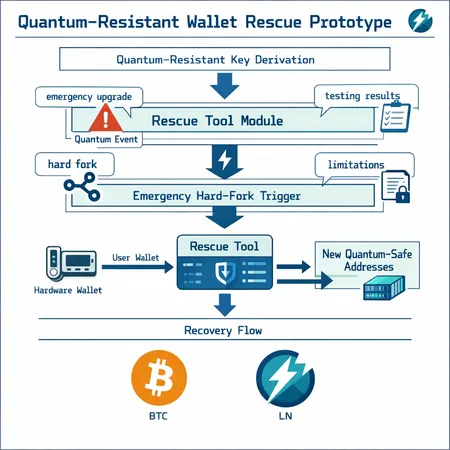
At a high level the rescue prototype is a pragmatic response to a narrow but severe scenario: imagine a credible report that a quantum computer can derive ECDSA private keys from observed public keys or signatures within a short window. In that event the Bitcoin network might coordinate an emergency upgrade (a hard fork or softening of rules) to introduce post‑quantum defenses or migration primitives. The immediate operational problem is this: before or during such a fork, funds sitting at addresses with exposed public keys could be stolen by adversaries who can compute private keys quickly. The rescue tool is intended to give honest users a way to sweep or migrate funds into safer, post‑upgrade key types even while the upgrade is being coordinated.
The developer framed the prototype as an emergency utility rather than a complete migration platform. It is explicitly experimental — a proof of concept that demonstrates one possible set of mechanics that would let users recover funds during a narrow window when the network enacts emergency rules.
Prototype architecture — components and high‑level mechanics
The prototype is best understood as a small stack of utilities and off‑chain procedures built to operate against a hypothetical network change. Key architectural elements include:
- Recovery transaction generator: software that can, given a seed or private key material, construct and pre‑sign the specific transactions needed to transfer funds into new outputs permitted by the emergency upgrade. These transactions are intended to be valid under the new rules that the fork would introduce.
- Coordination logic: a workflow for determining which addresses need rescue (for example, monitoring UTXOs whose public keys have been exposed), batching operations to minimize on‑chain footprint, and deciding when to broadcast.
- Safe signing path: guidance and tooling to sign or authorize sweeps in a way that minimizes exposure. In practice that often implies performing sensitive signing inside isolated, audited environments or hardware devices rather than on commodity endpoints.
- Broadcast and monitoring tooling: to push rescue transactions during what could be a congested, contentious fork window and to watch for competing (adversarial) transactions.
In plain terms, the rescue tool produces the right transactions for the changed rules and helps users broadcast them as quickly and reliably as possible.
How recovery would work in a hypothetical quantum‑event hard fork
A plausible rescue flow (conceptual):
- The network signals and deploys an emergency rule set that, for example, introduces a new output type or accepts pre‑authorized migration transactions.
- Users run the rescue software locally (or custodians run it centrally) to generate transactions that move funds from legacy addresses to new, post‑quantum output formats.
- The rescue transactions are broadcast and confirmed. Monitoring tools watch for adversarial attempts to spend the same UTXOs; in many architectures, time‑locks or other ordering primitives help prioritize honest migration.
The prototype demonstrates these mechanics in a controlled test. It does not invent a magical cryptographic substitute; rather it provides a practical migration workflow that can operate under emergency conditions.
What the developer tested and the stated limitations
According to the primary report by Lightning Labs’ CTO, the prototype was built and exercised as a proof of concept. The developer stressed several important caveats:
- Experimental code: this is prototype software, not production‑grade tooling. It needs security audits and hardening before any real‑world use.
- Coordination dependency: the tool assumes a coordinated network upgrade — a political and technical process that is non‑trivial. Its utility depends on the specifics of any emergency fork’s ruleset.
- No full protection for all wallets: wallets that continuously reuse public keys or reveal public keys before spending are inherently more exposed; rescue mechanics may only be effective for certain address types and patterns. Hardware wallets and custodial setups that do not support the necessary signing paths would need updates.
- Operational risk: broadcasting many migration transactions during a fork risks congestion, chain reorgs, and race conditions with adversaries. The tool reduces but does not eliminate these risks.
The developer deliberately framed the prototype as a stimulus for discussion — an invitation to the ecosystem to design coherent migration and upgrade playbooks rather than a final product.
(Details of the prototype and the developer’s own notes on testing are summarized in the public write‑up.) (Lightning Labs CTO prototype article)
Why an emergency upgrade might be required
Emergency upgrades would be on the table if a credible quantum attack vector materially reduced the time between public‑key exposure and private‑key compromise. Two related drivers could push the network toward a hard fork:
- A demonstrated quantum algorithm or system that can recover private keys from ECDSA public keys at useful time scales.
- Rapid exploitation campaigns that begin stealing funds from obvious targets, creating market panic and a strong incentive to change consensus rules quickly (for example, by introducing post‑quantum signature schemes or migration primitives).
Network upgrades of this nature are politically and technically fraught. They require broad consensus or at least movement by a sufficient portion of the relay and mining ecosystem. But the possibility — however unlikely today — motivates the rescue prototype: if an emergency fork becomes necessary, tools to move funds safely under the new rules are vital.
Counterarguments: why some think quantum risk is overblown
Not everyone agrees that preparing aggressive emergency migration tooling should be a top priority. Michael Saylor has publicly argued that Bitcoin likely bottomed and that quantum risk is often overstated, suggesting the practical threat horizon is long and speculative (The Block summary of Saylor’s view). Key counterpoints include:
- Engineering timelines: building a quantum computer capable of breaking ECDSA at scale remains an enormous engineering challenge. Estimates from credible groups typically place such capability years or decades away.
- Defensive window: the Bitcoin ecosystem has time to observe, test, and implement post‑quantum primitives before an existential breach occurs, especially because widespread exploitation requires both computing power and operational coordination by an attacker.
- Mitigations already in practice: sound key hygiene (avoid exposing public keys pre‑spend, prefer P2SH/P2WSH where appropriate, avoid key reuse) substantially reduces risk for many users today.
Saylor’s position is useful tempering: it cautions product leads against disproportionate distraction from more immediate security concerns (social engineering, hardware wallet bugs, custody operational failures). That said, dismissing quantum planning entirely ignores plausible worst‑case operational scenarios that large custodians cannot afford to ignore.
Operational implications for custodians and hardware‑wallet vendors
If you run a custodial service, exchange, or produce hardware wallets, the prototype and the surrounding debate translate to concrete programmatic actions:
- Cryptographic agility: design systems so key‑management and signing logic can be upgraded without requiring users to migrate private keys urgently. Abstract signing modules and use modular key derivation so new schemes can be adopted.
- Firmware and software update paths: ensure devices and clients can receive timely, authenticated updates. Test rollback and recovery workflows thoroughly.
- Emergency playbooks and drills: have a documented, tested plan for an emergency network upgrade including communication templates, migration tooling, batching/broadcast strategies, and legal/compliance checklists.
- Key exposure minimization: avoid address reuse, prefer native SegWit scripts that reveal fewer on‑chain pubkeys, and consider pre‑spend best practices when building UX flows.
- Interoperability testing: run testnet drills of any migration tooling you might need. The prototype demonstrates why coordinated testing matters: behavior during a real fork can be surprising.
- Customer communications: prepare messaging for retail customers that balances calm guidance with actionable directions (e.g., how to rotate funds if needed).
For hardware‑wallet vendors the critical pieces are secure firmware signing, a fast and auditable update channel, and clear guidance to users about when and how to install emergency migrations. Custodians need additional operational capacity: secure signing enclaves, hot/cold coordination, and throughput to broadcast mass sweeps under pressure.
Practical checklist: when and how wallet providers and long‑term BTC holders should act
Immediate (now)
- Inventory: catalog which address types you support, where public keys are exposed, and which flows reuse keys.
- Backups and continuity: verify secure seed backups and recovery processes for all critical accounts and devices.
- Monitoring: subscribe to credible quantum‑research feeds and set thresholds for alerts (e.g., public demonstrations of quantum key‑recovery on ECDSA).
- Hardening: stop new engineering projects that knowingly introduce on‑chain key exposure or long‑lived public‑key reuse.
Short‑to‑mid term (6–24 months)
- Cryptographic agility plan: modularize signing stacks and define the process for introducing post‑quantum algorithms.
- Testnets and drills: run periodic testnet migrations that simulate an emergency fork and exercise your rescue/broadcast tooling.
- Vendor coordination: establish channels with hardware wallet vendors and custodial partners to coordinate firmware updates and migration tooling.
- Customer education: prepare clear, low‑friction migration instructions for different user segments (retail vs institutional).
Long term (strategy)
- Research and adoption: track standardized post‑quantum signature schemes, contribute to open‑source implementations, and plan conservative adoption timelines once standards mature.
- Legal and compliance: work with counsel on authority to act in an emergency fork, particularly for custodians who may need to move customer funds under extraordinary network changes.
- Capacity planning: ensure you have the signing throughput, monitoring, and distribution infrastructure to execute large‑scale sweeps if required.
Balancing preparedness with perspective
The Lightning Labs CTO prototype is valuable because it shifts the conversation from abstract panic to concrete engineering: what would a rescue workflow actually look like, and what operational pieces must exist for it to work? That is useful even if one accepts Michael Saylor’s more relaxed timeline for quantum risk. In practice, the right posture for technical product leads and advanced BTC holders is a balance: invest in cryptographic agility, incident response playbooks, and monitoring — but avoid expensive, disruptive migrations until standards and threat signals justify them.
For teams building on BTC and Lightning, the prototype is a useful blueprint for a narrowly scoped emergency toolset, not a replacement for long‑term post‑quantum planning. Custodial platforms and hardware vendors should incorporate rescue drills into broader operational readiness exercises; retail and long‑term holders should focus on good key hygiene and sensible backups today.
Bitlet.app and other service operators will benefit from pragmatic preparedness: design for safe upgrades and clear user flows, while monitoring the science so any major migration is deliberate, coordinated, and minimally disruptive.
Sources
- Lightning Labs CTO prototype coverage: Bitcoin.com report on the quantum‑resistant wallet rescue prototype
- Counterpoint on risk framing: The Block summary of Michael Saylor’s view on quantum risk