Aave CAPO Oracle Glitch: Technical Post‑Mortem, Governance Lessons, and Risk Mitigations
Summary
Executive summary
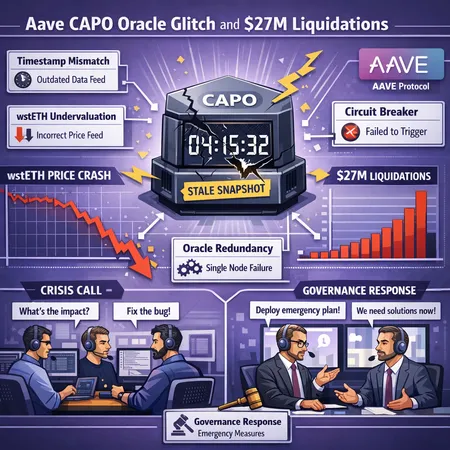
On March 11, 2026, a configuration error in Aave’s CAPO oracle led to a rapid undervaluation of wstETH that produced roughly $27 million in liquidations across the protocol. The error appears to have been a stale‑snapshot vs. timestamp mismatch: the oracle returned an outdated snapshot (or failed to validate update timestamps), making wstETH look far cheaper than its market value. Aave stepped in to cover remaining bad debt while the community and engineers worked to patch the feed. This post‑mortem explains the technical root cause, reconstructs the liquidation timeline, and offers practical engineering and governance mitigations for future resilience.
For risk teams and DAO governors reading this, the incident is a reminder: price feeds are not “plumbing” you can treat as infallible. They are a core part of financial security and must be designed, tested, and governed as such. For many readers, the lessons here overlap with other oracle incidents — but the CAPO case shows how subtle configuration errors become systemic if not caught quickly.
Background: CAPO, wstETH, and why this mattered
Aave relies on CAPO (the protocol’s configured price oracle aggregator) to price assets used as collateral and to compute health factors for borrowers. wstETH is a wrapped token representing staked ETH; it’s widely used as collateral because it tracks staked ETH yield and principal.
When an asset like wstETH is mispriced low, borrowers who used it as collateral can instantly become undercollateralized. Automated liquidators then seize collateral and trigger on‑chain liquidations. Because DeFi liquidations are automated and mechanical, a momentary oracle glitch can cascade into outsized, near‑instant losses.
The CAPO incident is a textbook example: a technical configuration mismatch caused the oracle to serve a stale or incorrectly timestamped price which undervalued wstETH. The resulting forced liquidations amounted to roughly $27M, per contemporaneous reporting, and Aave ultimately intervened to cover residual losses while governance worked on mitigations Cointelegraph report and analysis Invezz analysis.
Technical root cause: stale snapshot vs timestamp mismatch and wstETH undervaluation
At a technical level, the problem boils down to a configuration and validation gap in CAPO’s update logic. The oracle pipeline involved periodic snapshots and timestamped price reports. A configuration parameter expected the feed to reject values older than a given timestamp or to fall back to an alternative feed; instead, CAPO occasionally served a stale snapshot without the expected freshness check. That created a mismatch between the feed's timestamp validation and the snapshot being used.
Concretely:
- The oracle pipeline accepted a snapshot that did not reflect the latest market price update. The snapshot's internal timestamp either was ignored or misinterpreted by the CAPO configuration.
- Because that stale snapshot reported a lower wstETH valuation than the prevailing market price, smart contracts that compute borrower health factors saw collateral values fall suddenly.
- Liquidation smart contracts executed quickly against those apparent undercollateralized positions, leading to rapid, automated liquidations across the protocol.
This is not merely an academic distinction. A stale snapshot versus an out‑of‑date timestamp is a behavioral/contractual mismatch: one is an off‑chain process failing to refresh data; the other is an on‑chain check failing to enforce freshness. In the CAPO case both checks were either missing or incorrectly set, so the stale data propagated to risk calculations.
Timeline of events and the liquidation cascade
- Shortly before the incident window on March 11, 2026, the CAPO pipeline failed to ingest or validate a fresh price update for wstETH.
- The oracle returned a priced snapshot with an older timestamp, which CAPO treated as valid due to configuration settings.
- Borrower health factors computed on the stale lower wstETH price immediately crossed liquidation thresholds for many positions.
- Automated liquidators — configured to act on-chain when health < 1 — executed en masse, generating the reported ~ $27M in liquidations.
- Aave governance and ops monitored the event and, after fast triage, intervened: they halted certain oracle‑dependent operations and used protocol resources to cover residual deficits while fixes were deployed. Coverage and step‑in details were reported as Aave stepping in to cover losses in the aftermath Cointelegraph report and examined in market commentary Invezz analysis.
The speed of liquidation execution—designed to protect the protocol—also means the first minutes of an incident are the most dangerous. That window is where pausing functionality, fallback oracles, or human intervention can prevent a cascade.
How Aave responded (operational and governance actions)
Aave’s response followed several threads: emergency operations to limit ongoing damage, parameter changes to reduce immediate exposure, and governance conversations about long‑term fixes.
Operationally, the team:
- Paused or tightened markets dependent on the CAPO feed to slow liquidation velocity.
- Deployed temporary fallbacks or manual price overrides where safe and auditable.
- Used the protocol’s treasury or insurance buffers to cover losses that remained after liquidators executed.
On the governance side, discussions focused on changing CAPO parameters (freshness thresholds, allowed rollback behavior), adopting redundant feeds, and accelerating audits of oracle configurations. These conversations are ongoing and illustrate the tension between decentralization (no single admin kill switch) and the need for fast, coordinated emergency responses.
Governance implications: short‑ and long‑term
Short term, DAOs must accept that oracles are a governance vector. Quick fixes—shortening allowed staleness windows, tightening collateral params for oracle‑sensitive assets, or temporarily disabling liquidations—are necessary to stop bleeding. But short fixes can create new risks (e.g., halting liquidations too long raises insolvency risk), so they must be bounded and transparent.
Long term, governance models should treat oracle resiliency as a first‑class risk domain:
- Any protocol relying on third‑party oracles should require multi‑source attestations and define minimum redundancy SLA in governance docs.
- Emergency powers need to be explicit, narrowly scoped, and ideally time‑boxed with on‑chain visibility so the community can audit responses after the fact.
- Oracles and their configurations should be subject to the same code review, bounty, and audit cadence as core smart contracts.
This event also changes how DAOs view counterparty risk: third‑party oracle providers should be evaluated not just for uptime, but for their integration complexity, timestamp semantics, and failure modes.
Recommended engineering mitigations
Below are practical, engineering‑first steps DeFi protocols and oracle providers should implement.
1) Oracle redundancy and multi‑source aggregation
Never trust a single feed. Aggregate across multiple trusted providers and compute a robust statistic (e.g., median of n feeds, trimmed mean) rather than a single source. For particularly sensitive assets (staked derivatives, wrapped tokens), require more redundancy and faster heartbeat checks.
2) Freshness checks and timestamp semantics
Enforce explicit on‑chain freshness checks: a price older than X seconds/minutes should be rejected or marked stale. But also validate that the timestamp attached to a snapshot aligns with the actual update cadence of the provider. In other words, compare both the feed's declared timestamp and the on‑chain receipt time.
3) Circuit breakers and liquidation throttles
Introduce circuit breakers that detect abnormal price deltas in short windows (e.g., >Y% in Z seconds) and either slow liquidator execution or route to a manual or fallback resolution. Throttling large automated liquidations reduces the chance of cascading rounds of forced selling.
4) Fallback oracles and graceful degradation
Define explicit, auditable fallback sources for each asset. If the primary aggregator fails freshness or consensus checks, fall back to a secondary aggregate or to a time‑weighted average price (TWAP) for a short emergency window.
5) Oracle audits and formal verification
Treat oracle config and validation logic as critical code. Regularly subject both provider code and the protocol’s integration logic to audits and, where possible, formal verification for key invariants (e.g., "do not accept prices older than X" or "do not accept rollback of token peg without consensus").
6) Monitoring, observability, and runbooks
Build high‑fidelity monitoring that includes feed freshness, timestamp drift, and cross‑feed divergence. Have runbooks for incidents that define who can act, what actions are permissible, and how to coordinate with governance and the community.
Protocol‑level mitigations and design principles
Engineering mitigations are necessary but not sufficient. Protocol design choices should anticipate oracle failure modes:
- Prefer collateral classes that are less oracle‑sensitive or combine oracle‑sensitive assets with overcollateralization margins.
- Introduce conservative exposure caps and concentration limits for assets whose pricing relies on single data semantics (e.g., tokenized derivatives like wstETH).
- Design liquidation incentives that account for market impact during oracle anomalies, including partial liquidations and capped slippage protections.
Bitlet.app and other service operators that rely on or offer lending features should treat these principles as part of product risk reviews.
How this should change DeFi risk models for users and DAOs
The CAPO incident demonstrates that oracle reliability must be explicitly modeled in risk frameworks. Practical changes include:
- Lowering effective LTVs for assets where the price depends on a single on‑chain feed or complex off‑chain staking abstractions.
- Adding an oracle‑failure stress scenario to capital and margin models that simulates a sustained stale feed combined with rapid liquidation activity.
- Requiring insurance or buffer funds for markets with high oracle sensitivity; building capital buffers into the protocol treasury to cover systemic oracle failures.
- Encouraging users to diversify collateral types and to understand that even liquid, blue‑chip assets can cause cascading liquidations if mispriced.
Risk managers should add oracle metrics (freshness violations per month, median feed delta vs market) into dashboards and KPI targets.
Practical checklist for DAOs and builders (quick reference)
- Implement multi‑source price aggregation and defend against single‑feed failure.
- Add timestamp and snapshot sanity checks that are auditable on‑chain.
- Build circuit breakers and liquidation throttles that are automatic and transparent.
- Create an incident runbook and test it with tabletop exercises; include clear roles for ops and governance.
- Require regular oracle integration audits and publish provider SLAs.
- Update risk models to stress test oracle failure modes and adjust LTVs accordingly.
Conclusion
The Aave CAPO oracle glitch is a clear, if painful, reminder that oracles are central to DeFi's security model. A stale snapshot or a timestamp mismatch is a small configuration mistake with outsized consequences. The protocol‑level reaction—pauses, fallbacks, and treasury interventions—mitigated immediate damage, but the incident should catalyze durable changes: more redundancy in oracle design, better on‑chain freshness checks, faster and more explicit governance emergency tools, and risk models that explicitly incorporate oracle failure scenarios.
For DeFi developers, risk managers, and DAO governors the path forward is straightforward in principle but requires sustained attention: treat oracle configuration as part of the protocol attack surface, elevate testing, and build governance and engineering controls that can act quickly without undermining decentralization.
Sources
- Cointelegraph — Aave CAPO oracle glitch and liquidations: https://cointelegraph.com/news/aave-capo-oracle-glitch-27m-liquidations?utm_source=rss_feed&utm_medium=rss&utm_campaign=rss_partner_inbound
- Invezz — Analysis of the Aave oracle glitch and token outlook: https://invezz.com/news/2026/03/11/aave-price-outlook-after-oracle-glitch-triggers-27-m-liquidations/?utm_source=snapi
(Internal reference: see discussions of on‑chain price sensitivity in DeFi governance threads and protocol risk docs for historical context.)


