$50M to $36K: Post-Mortem of the March 2026 CoW Protocol Slippage Disaster
Summary
Executive summary
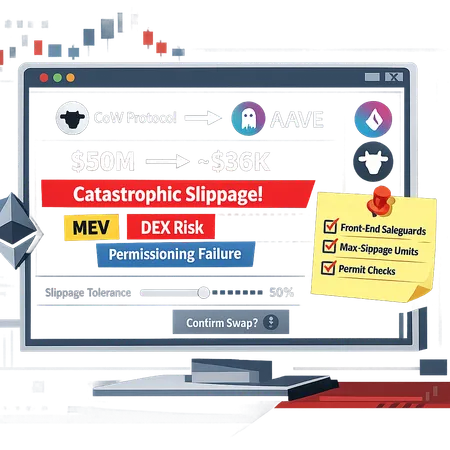
In March 2026 a trade that originated as a roughly $50 million intent to swap into AAVE was executed via the CoW Protocol ecosystem and ended up netting only about $36,000 — a near‑total loss. Media outlets, including Finbold and TheNewsCrypto, published a timeline and a technical post‑mortem. The immediate cause was extreme slippage compounded by UX/permissioning breakdowns and adverse interactions with routing and MEV mechanics. This article explains the how and why, and then prescribes engineering and operational mitigations for traders, custodial wallets, and protocol designers.
What happened: timeline and high‑level causes
According to initial reporting, an order intended to swap a very large notional into AAVE was routed through CoW Protocol’s matching and settlement system. Rather than executing at a price close to market, the swap suffered enormous price impact during routing and settlement — leaving the trader with roughly $36K worth of AAVE instead of the expected multimillion dollar position. TheNewsCrypto and Finbold provide the basic timeline and transaction data; their writeups suggest the root causes were a mix of user settings, frontend confirmation gaps, and on‑chain execution path choices that allowed extreme slippage.
Two immediate themes emerge: (1) execution logic and routing produced massive price impact, and (2) front‑end and permissioning UX allowed execution without sufficient human or programmatic safeguards. Both themes are common in high‑notional failures but their coupling here created a catastrophic result.
How slippage ballooned: liquidity, routing and CoW mechanics
Slippage is fundamentally the gap between quoted price and execution price caused by consuming liquidity. For very large market trades, thin liquidity at the quoted venue means the order walks the book and pays exponentially worse prices. Aggregators and matching engines attempt to split and route across venues to minimize impact, but they also introduce complexity:
- Aggregation and routing may traverse multiple DEX pools (AAVE liquidity, AMM pools, orderbooks). Each hop compounds price impact if liquidity is shallow.
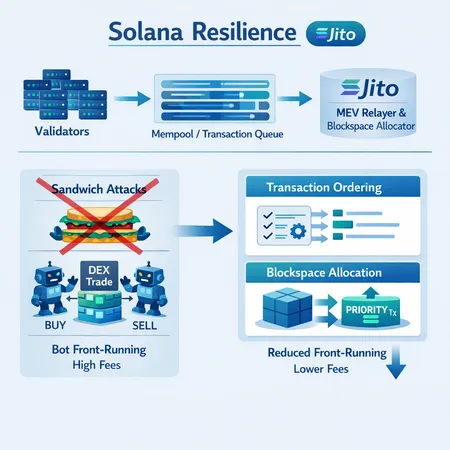
- CoW Protocol (COW) operates by off‑chain matching and on‑chain settlement; this design can reduce simple frontrunning but still relies on proper matching and fallback routing if initial liquidity is insufficient.
- In this incident, execution paths appear to have left the transaction exposed to extremely adverse price steps during settlement — the effective result was that most of the notional was executed at far worse prices than the user anticipated.
CoW’s batch/matching model helps mitigate some MEV strategies, but it does not magically eliminate price‑impact risk if the order is mispriced relative to available liquidity. When a large swap tries to consume liquidity deeper than markets can supply, the residual becomes tiny or worthless relative to expectations.
MEV, front‑running and back‑running interactions
MEV (Miner/Maximal Extractable Value) is often villainized as only enabling sandwich attacks, but here MEV manifests as a set of ordering, backrun, and settlement‑ordering problems. Key points:
- Private matching or batch settlement (as with CoW) can limit public mempool sandwich attacks, but if settlement requires on‑chain liquidity routing into AMMs, those on‑chain steps remain vulnerable.
- Adversarial actors and relays can still reorder or exploit poor price windows when a transaction exposes a large delta between expected and available prices.
- TheNewsCrypto’s post‑mortem suggests routing and slippage allowed on‑chain interactions to be executed at extreme prices; opportunistic MEV actors and liquidity takers may have amplified the impact.
In short: CoW reduces some classes of MEV but does not remove the fundamental economics of slippage when liquidity is insufficient. Large exposure plus poor pre‑trade limits is still the recipe for disaster.
UX and permissioning failures that enabled the loss
Technical plumbing matters, but human interfaces and permission models were decisive here. Common failures observed in this kind of collapse include:
- Silent defaults: slippage tolerance sliders set too high by default or inherited from previous small trades. A 50,000% tolerance on a $50M order is lethal.
- One‑click trade patterns that lack a staged, contextual confirmation for outsized notional sizes.
- Poor visibility of expected price impact and worst‑case executed price; many UIs show a single mid‑price quote and a tiny percent impact that belies the real depth of the pools used.
- Insufficient permission scopes: wallets giving broad approvals without per‑trade whitelists or per‑counterparty constraints.
- No institutional risk guardrails: custodial desks or multisig flows that allow single approver execution for high‑value trades.
UX failures turn technical edge cases into catastrophic real losses. Trading interfaces should treat big trades differently—explicitly, loudly, and with friction.
Exchange/DEX counterparty warnings and settlement behavior
A large institutional trade often relies on counterparties (aggregators, DEX routers, relayers). Key risks to watch for:
- Router fallbacks: when a primary route fails, fallback to another route (or a sequence of atomic swaps) can dramatically worsen slippage. Front‑ends should lock routing or require re‑approval when fallback routing is invoked.
- Quote validity windows: many systems provide soft quotes that can become invalid between quote and settlement; when not enforced, the actual on‑chain swap can execute at much worse prices.
- Liquidity fragmentation: AAVE markets and AMM pools may hold aggregate depth, but splitting across pools can increase path complexity and price variance.
Exchanges and DEX routers must emit clear warnings, and custodial desks should require signed, time‑bound quotes for large notional trades.
Hardening front‑ends: practical UI/UX controls
Design patterns builders should adopt to prevent similar losses:
- Default conservative slippage caps: For example, set a platform default max slippage to 0.5% for retail by default and require an explicit multi‑step opt‑in (with typed confirmation) above thresholds (e.g., >1%).
- Dynamic impact warnings: show both expected price impact and worst‑case executed price based on available on‑chain liquidity depth. Flag when the worst‑case exceeds X% of notional.
- Size‑aware workflows: if a trade exceeds a percentage of 24h volume for a token or >Y% of a pool’s depth, surface a mandatory review step and require manual approval.
- Per‑trade approval scopes: require wallets to approve exact amounts, not infinite approvals; when fallback routes are used, request fresh confirmation.
- Simulated dry runs: run an on‑chain dry‑run or simulation of the execution path on behalf of the user and present the simulation result (gas + price + slippage) before final confirmation.
- Multi‑factor confirmations: large trades should require an explicit typed confirmation (e.g., type the notional), multi‑sig, or an out‑of‑band approval step.
These patterns reduce the chance that a trivial UI misclick or legacy slider setting becomes catastrophic.
Smart contract and protocol safeguards
Front‑end fixes are necessary but insufficient. Builders should add on‑chain and off‑chain controls:
- On‑chain slippage ceilings: smart contracts that abort if executed price deviates beyond a functionally small threshold unless explicitly allowed through a permissioned escape hatch.
- Permissioned execution modes: support limit‑only on‑chain execution by default for large notional trades—market‑like fills must be opt‑in.
- Time‑bound quotes and relay attestations: include signed attestations from relayers about quote validity windows and tool checks that settlement occurs only against those attestations.
- Whitelisting and rate limits for relayers: require relayers to register and adhere to rate limits and pre‑declared liquidity sources.
- Audit and simulation suites: every new router or matching change should include regression tests for corner cases (very large notional vs pool depth).
These contract‑level guardrails make it harder for a UI slip or a routing fallback to become irreversible loss.
Operational playbook for custodial wallets and institutional desks (checklist)
Use this checklist before approving large on‑chain swaps:
- Pre‑trade simulation: run an on‑chain simulation (not only off‑chain quote) showing expected execution price and worst‑case slippage.
- Hard slippage caps: enforce organization policy (e.g., max 1% slippage for spot trades >$1M) implemented at both client and custody layers.
- Quote signing: require time‑bound, signed quotes from counterparties or aggregators; do not accept soft quotes without attestations.
- Multi‑sig and dual control: require >1 approver for trades above thresholds; use hardware signing where possible.
- Limit approvals: avoid infinite token approvals; prefer per‑trade allowance resets and narrow approval scopes.
- Liquidity sanity checks: compare the trade size against on‑chain pool depth and 24h volume; flag trades >X% of depth for review.
- Fallback policy: disable or require manual approval for router/relayer fallback routes on large trades.
- Post‑trade reconciliation: immediate on‑chain reconciliation and settlement confirmation; trigger incident playbook on abnormal outcomes.
This checklist is operational; integrating it into approval UIs and signature flows materially reduces exposure.
Example UX pattern: staged approval flow
A recommended front‑end workflow for trades above a threshold (e.g., >$250k):
- Quote and simulation: show aggregated quote + dry‑run results, including worst‑case price.
- Typed confirmation: require the user to type the notional amount and a single sentence acknowledging slippage risk.
- Secondary approval: if institutional, require a second signer or a compliance approver.
- Final browser wallet sign: present exact calldata and require user wallet approval for precisely that calldata (no infinite approvals).
This pattern adds friction but prevents accidental, irreversible mistakes.
Why CoW Protocol didn’t alone prevent this
CoW Protocol reduces specific MEV vectors by doing off‑chain matching and atomic settlement, but it cannot change the reality of market depth and routing consequences. The protocol helps against simple sandwich attacks, yet when an order is mispriced against available liquidity, there is no protocol magic that converts insufficient liquidity into a better price. In other words, CoW mitigates some execution risks but is not a substitute for prudent UX, permissioning, and institutional controls.
For teams building on such primitives, the right approach is complementary: use batch matching and private relays to reduce extraction, but also build conservative front‑end guardrails and on‑chain ceilings so liquidity mismatches cannot turn into complete loss.
Recommendations summary for traders and builders
- Default to conservative slippage tolerances and require explicit opt‑in for aggressive settings.
- Implement size‑aware UI flows and mandatory manual review for outsized trades.
- Simulate execution paths on‑chain and show worst‑case outcomes before signature.
- Limit approvals and prefer per‑trade allowances; require updated approvals if routes change.
- Add on‑chain abort conditions for excessive price deviation and signed quote attestations.
- For institutional desks: multi‑sig, dual approval, and signed time‑bound quotes should be mandatory.
Platforms such as Bitlet.app and venue front‑ends should embed these primitives into their UX and custody integrations so that new users are protected and institutions have enforceable policy controls.
Conclusion
The March 2026 $50M→$36K event is a painful reminder that execution risk is not just a protocol problem — it is a system problem spanning UX, permissioning, routing logic, MEV dynamics, and custodial procedures. CoW Protocol provides powerful tools to reduce certain MEV vectors, but it cannot eliminate slippage driven by insufficient on‑chain liquidity or human/UX mistakes.
Protocol designers and trading desks must treat large trades differently: require simulations, staged approvals, on‑chain guardrails, and explicit, conservative user defaults. When these layers work together, the odds of turning a multi‑million dollar intent into a near‑total loss fall dramatically.
Sources
- Finbold — initial report on the $50M swap: https://finbold.com/crypto-trader-accidentally-swaps-50-million-for-36000-aave-in-a-minute/?utm_source=snapi
- TheNewsCrypto — detailed post‑mortem on slippage and CoW mechanics: https://thenewscrypto.com/50m-crypto-trade-turns-into-36k-after-massive-slippage-on-aave-and-cow-protocol/?utm_source=snapi
For wider context on on‑chain market dynamics, many traders still look to DeFi liquidity patterns and, for macro correlation, markets like Bitcoin as bellwethers when sizing execution risk.