Inside the £172M Home-Camera Seed-Phrase Theft: How High-Net-Worth Crypto Keys Are Compromised and Reclaimed
Summary
Executive summary
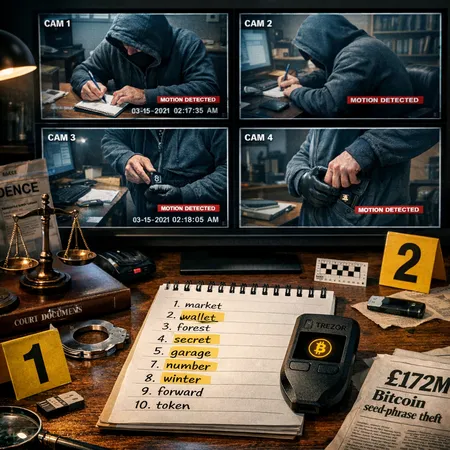
The coming trial surrounding the alleged theft of 2,323 BTC — reported at roughly $172M — has focused attention on a simple but devastating reality: hardware wallets can be outmaneuvered when real-world operational security is broken. The indictment described alleged covert home surveillance that captured seed-recovery material and allowed the attackers to drain funds. For family offices, high-net-worth individuals and custody providers, the lesson is blunt: device security matters, but human and environmental security matter more.
For many readers, Bitcoin remains the primary asset at risk, and the case underlines how custody decisions, physical security, and legal preparedness must be coordinated. This article investigates the mechanics alleged in the case, breaks down common hardware-wallet attack vectors, assesses legal remedies and precedent, and delivers an actionable defensive checklist for sophisticated holders and exchanges offering custody.
Why hardware wallets are necessary but not foolproof
Hardware wallets like Trezor were designed to keep private keys off internet-connected machines. They reduce many attack surfaces but cannot eliminate risks that start outside the device: seed exposure during setup, compromised backup materials, and targeted surveillance. A hardware wallet's security assumptions include that the user keeps the recovery seed secret and that the physical environment where setup or recovery happens is free from observers — visible or covert.
Attackers exploit that human dependency in numerous ways. Social engineering — impersonation, pressure tactics, or seemingly legitimate requests for help — can trick custodians into revealing or exposing seeds. Supply-chain threats, tampered packaging, or malicious firmware (less common for open-source devices like Trezor but still plausible via peripherals or compromised computers) expand the attacker toolkit. The most striking recent allegation is that covert home cameras were used to record recovery words, then transcribe and reassemble them offsite, enabling the transfer of funds without ever touching the victim's device.
What the trial alleges: the mechanics in the Ping Fai Yuen case
According to reporting on the case, prosecutors allege a systematic operation: covert cameras placed in a property captured footage of seed phrases and recovery steps, which were then used to reconstruct the victim's keys and move funds. Detailed reporting on the indictment and trial timeline can be found in the investigative piece that first exposed the use of home cameras in this theft here.
Key elements alleged in the case include:
- Physical surveillance: hidden or disguised cameras placed to view desks, safes, or paperwork where recovery seeds or PINs were handled.
- Documentation capture: high-resolution footage or stills that allowed attackers to read recovery words, partial PINs, or passphrase entry patterns.
- Offsite reconstruction: aggregating captured fragments, validating guesses against public on-chain activity, and then seeding a wallet to extract funds.
The reported scale — thousands of BTC — is a reminder that once a seed (or an effective passphrase) is captured, control of the private keys is immediate and absolute. Chain analysis can help trace the movement after the fact, and exchanges become crucial nodes for recovery if attackers attempt to cash out through regulated venues.
The broader custody context: why institutional demand changes risk calculus
Institutional adoption and ETF flows have pushed custody into the spotlight. Growing institutional demand increases the volume and velocity of large transfers and raises both the incentive for targeted thefts and the need for robust custody operations. Coverage of the institutional accumulation trend highlights why custody practices are evolving as ETFs and institutions accumulate Bitcoin.
As custodians handle larger balances, attackers shift from opportunistic theft to carefully planned operations. That changes both the adversary profile — from lone opportunists to organized groups — and the stakes for legal and operational protections.
Legal remediation: what victims can (and can't) expect
When a seed phrase is stolen and funds move on-chain, legal remedies exist but face real limits. Here are practical steps and their usual outcomes:
Rapid evidence preservation: Immediately preserve physical evidence (cameras, devices, logs) and secure any surveillance footage. Forensically preserve computers and phones. Law enforcement cooperation is essential; delays reduce chances of asset recovery.
Contact exchanges and custodians: If attackers route funds through centralized exchanges, rapid notices, and freeze requests — backed by court orders or law enforcement cooperation — can result in temporary holds and potential recovery. Exchanges’ AML/KYT tools and compliance teams are often the most effective stopgap.
Civil claims for conversion and injunctions: Victims can sue to freeze identifiers (account numbers, fiat proceeds) and obtain asset preservation orders. Civil remedies can secure funds that have been converted into traceable fiat or other assets.
Criminal prosecution: Where evidence supports it, prosecutors can pursue theft, fraud, and conspiracy charges. Conviction can lead to asset forfeiture in some jurisdictions, but success depends on cross-border cooperation when funds transit multiple jurisdictions.
Limits of on-chain remedies: Once private keys are used to transfer funds on-chain, the ledger enforces the transfer; there is no built-in reversal. Chain analysis helps trace flows, but recovering coins depends on where they end up and the cooperation of custodial intermediaries.
Recent reporting on the case illustrates how criminal investigation and civil work must run in parallel. The Blockonomi article covering the home-camera allegations walks through the indictment detail and provides context for the evidentiary claims here.
Precedent and practical expectations
There are successful precedents where victims reclaimed value through exchange cooperation and court orders, but there are also many cases where coins moved into privacy mixers or wallets controlled by non-cooperative actors and were never recovered. Expect the following practical realities:
- Speed matters. The faster victims and counsel engage exchanges and law enforcement, the higher the chance of recovery.
- Jurisdictional friction is real. Cross-border tracing and MLATs slow the process.
- Insurance and contractual remedies help. Carefully drafted custody agreements, insurance policies, and SLA clauses with custodians give victims contractual leverage and, in some cases, monetary relief.
Practical defenses for high-net-worth holders and family offices
Layered defenses turn a single point of failure (the seed phrase) into multiple hurdles. The following controls are practical, measurable, and designed for wealthy holders who face targeted threats.
Operational & physical security
- Never create or enter seeds on camera-visible surfaces. Disable or remove cameras (including smart-home devices) when performing any wallet setup or recovery.
- Use secure, supervised locations for signing/recovery. Consider a dedicated, camera-free room with tamper-evident seals and restricted access.
- Conduct regular counter-surveillance sweeps. Hire physical-security firms to check for hidden recording devices or signals indicating covert cameras.
- Maintain two-person rules for sensitive operations. Require two authorised signers/observers during recovery or large transfers to reduce coercion risks.
Seed storage and cryptographic hardening
- Store recovery seeds in durable, fire/impact-resistant metal backups and split copies across geographically separated, trusted custodians.
- Use passphrases (the optional 25th word) to add an additional secret layer; store the passphrase separately from the recovery words.
- Adopt multisig setups (e.g., 2-of-3, 3-of-5) using diverse key-generation vendors. Multisig elevates the operational burden on attackers because they must capture multiple independent secrets.
- Consider Shamir Secret Sharing or SLIP-0039 for threshold backups rather than a single linear mnemonic.
Device and supply-chain security
- Buy hardware wallets directly from manufacturers or verified resellers; avoid second-hand devices.
- Verify device fingerprints and firmware integrity against manufacturer guidance. Prefer devices with tamper-evident packaging and secure elements where appropriate.
- Use air-gapped signing devices and dedicated, hardened signing machines; avoid connecting signing devices to the internet except during known, controlled transfers.
Digital hygiene and social engineering defenses
- Train staff and family members on social engineering scenarios and create strict verification protocols for any contact requesting transaction approvals or recovery assistance.
- Segregate roles: the person who manages physical backups should not also be the person executing transactions.
- Keep an audit trail and immutable logs for all custody-related operations, and review them regularly.
Insurance, contractual, and governance controls
- Obtain tailored crypto insurance with clear definitions of covered perils (theft, social engineering, physical compromise).
- For family offices, create a custody governance policy: defined signers, access matrices, incident response plans, and external counsel and forensic vendors on retainer.
- Maintain an up-to-date recovery playbook: evidence preservation checklist, law enforcement contacts, and exchange escalation paths.
Custody alternatives for large holders and recommendations for exchanges
No single custody model fits all. Here are the tradeoffs and recommendations:
- Self-custody with enhanced controls: best for those who can maintain operational discipline. Use multisig across geographically and administratively independent signers.
- Regulated custodians: transfer operational burdens to a specialist with insurance, compliance programs, and insured hot/cold split. Ensure SLAs and proof-of-reserves disclosure if relevant.
- Hybrid custody: combine a regulated custodian for settlement liquidity and a self-custody multisig for long-term holdings.
For exchanges and custodial businesses, institutional-grade controls are essential:
- Implement robust cold-storage architectures with geographically isolated vaults, hardware security modules (HSMs) and multisig thresholds.
- Maintain strict out-of-band approval processes for large withdrawals and partner with world-class AML/KYT solutions to detect structuring or laundering behaviors.
- Offer customer education and optional custody tiers that allow clients to mandate multisig participants or custody-only access with contractual guarantees.
- Prepare legal playbooks for rapid freeze requests, and invest in investigative teams (or vendor partnerships) that can triage large thefts and coordinate with law enforcement.
Bitlet.app and other platforms in the custody ecosystem are part of that broader shift toward offering flexible custody options that combine automation with human oversight.
Incident response: what to do if you suspect a seed compromise
- Stop all sensitive operations. Power down and secure devices suspected of being observed or tampered with.
- Preserve evidence. Photograph and forensically image cameras, storage media, and surrounding areas. Record chain-of-custody.
- Notify exchanges and custodians with transaction hashes or identifying information so they can monitor or freeze flows.
- Engage expertise immediately: blockchain forensic analysts, physical-security firms, and counsel experienced in cross-border asset recovery.
- File reports with relevant law enforcement and prepare civil filings for injunctive relief if there is evidence funds are being moved to identifiable accounts.
Conclusion: security is organizational, not just technical
The alleged home-camera theft case is a warning to the entire ecosystem: hardware wallet security is a necessary technical layer, but it will not protect holders who ignore physical and human risks. For high-net-worth individuals and family offices, the right approach is layered: operational discipline, cryptographic hardening (multisig and passphrases), vetted custodial relationships, and legal readiness.
Speed and preparation increase the chance of recovery; complacency magnifies loss. Organizations that treat custody as a combined operational, legal, and physical-security problem will be far less attractive targets.
Sources
- Detailed reporting on the trial alleging covert home surveillance and seed-phrase theft: Home security cameras used to steal $172M in Bitcoin — trial set to begin.
- Context on growing institutional demand, ETFs, and custody needs as institutions accumulate Bitcoin: Bitcoin price climbs as global markets shake — ETFs and institutional buying.